
Choosing between a blockchain-based VPN and a traditional VPN comes down to understanding how each impacts your privacy. Here's a quick breakdown:
Traditional VPNs rely on centralized servers owned by a single company. While they encrypt your traffic, they require trust in the provider’s "no-logs" policy, which can be hard to verify. Centralized systems are also vulnerable to breaches, legal demands, and monitoring risks.
Blockchain-based VPNs (dVPNs) operate on decentralized networks, routing your traffic through multiple independent nodes. This design minimizes trust requirements, enhances anonymity, and makes tracking nearly impossible. Payments are handled via cryptocurrency, avoiding personal data like emails or credit card details.
Quick Comparison
Feature | Traditional VPNs | Blockchain-Based VPNs (dVPNs) |
|---|---|---|
Network Structure | Centralized servers | Decentralized peer-to-peer nodes |
Logging | Trust in provider’s policy | No central logs possible |
Anonymity | Requires personal details | Web3 wallet, no personal data |
Routing | Single-hop | Multi-hop (3–6 nodes) |
Censorship Resistance | Moderate (vulnerable to blocks) | High (global node diversity) |
Payment | Credit card or PayPal | Cryptocurrency only |
Blockchain-based VPNs are ideal for users prioritizing privacy, especially in high-risk or censored environments. Traditional VPNs are simpler to use but require trust in the provider. If privacy is your top concern, dVPNs offer a stronger, trustless alternative.
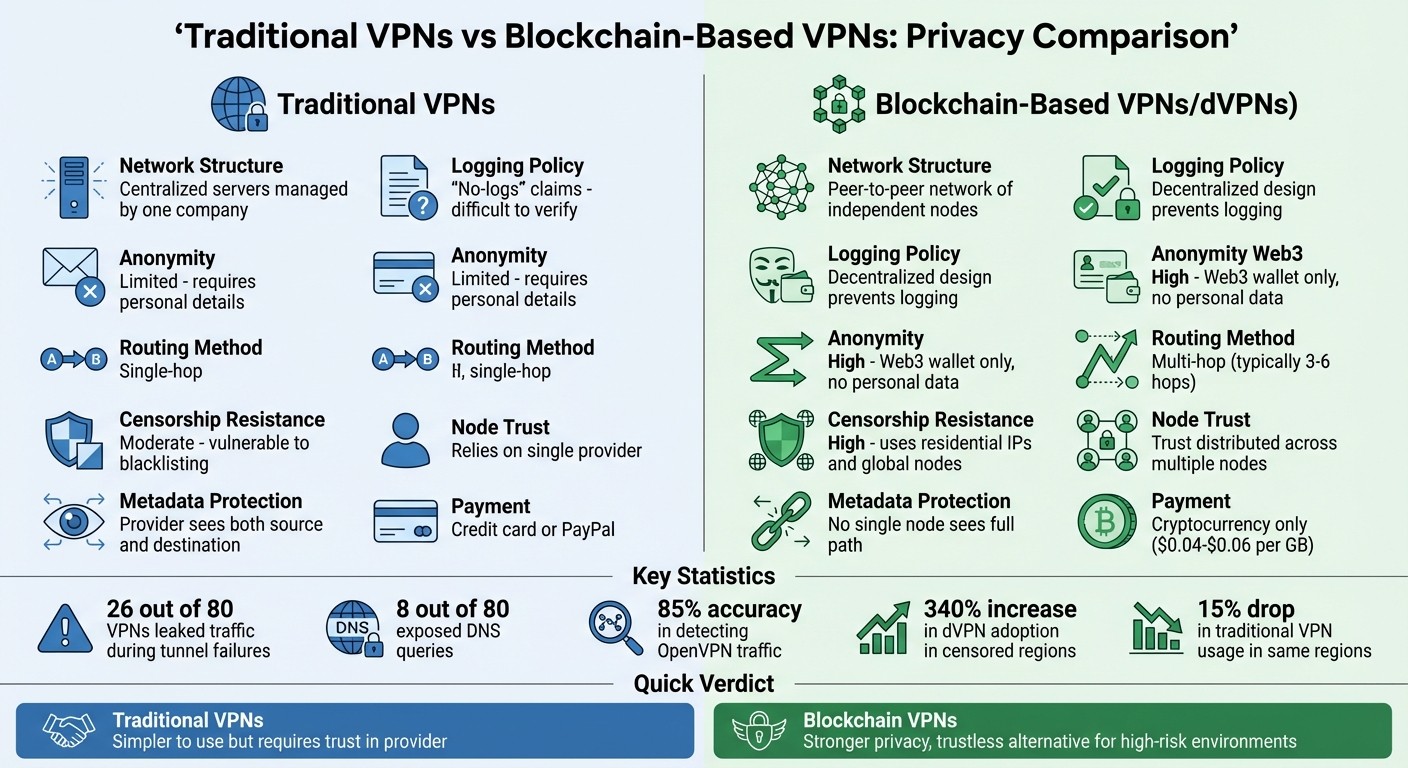
Traditional VPN vs Blockchain VPN Privacy Comparison
Privacy Risks in Traditional VPNs
Centralized Logging Creates Data Risks
Traditional VPNs rely on routing your internet traffic through a single company's servers. This setup often allows the provider to log your online activity, even if they claim to have a "no-logs" policy. Centralized infrastructures inherently carry monitoring risks - your data is funneled through one point, making it susceptible to breaches, government demands, or even misuse by the company itself. A 2022 study called "VPNalyzer" revealed concerning statistics: out of 80 desktop VPNs analyzed, 26 leaked traffic during tunnel failures, and 8 exposed DNS queries when connections dropped. These leaks could leave your browsing activity visible to your ISP, directly threatening your privacy.
The Trust Problem with VPN Providers
Using a traditional VPN shifts the trust burden from your ISP to the VPN provider. As Cube1214 aptly notes:
"Trust simply moves from your ISP to the VPN provider."
This means your VPN provider could potentially access the same sensitive data your ISP would have seen. Even providers with "no-logs" policies may be subject to legal jurisdictions requiring them to hand over user data. Additionally, many VPN servers are hosted in third-party data centers, introducing another layer of risk as these centers could monitor the data flowing through them. On top of this, advanced techniques like deep-packet inspection allow network operators to identify encrypted OpenVPN traffic with over 85% accuracy. This means that simply using a VPN can make your activity detectable, undermining its promise of privacy.
Single Points of Failure
Centralized servers also create a single point of failure. If a server is compromised, it can expose all the data routed through it. Unlike distributed systems, which spread traffic across multiple independent nodes, traditional VPNs rely on a single infrastructure. This setup increases the risk of widespread data breaches, making your online privacy even more vulnerable.
How Blockchain-Based VPNs Improve Privacy
No Central Logs or Servers
One of the biggest privacy risks with traditional VPNs is their centralized structure. Your internet traffic is routed through a single company's servers, which means that company could log or monitor your activity. Blockchain-based VPNs (dVPNs) eliminate this vulnerability by distributing traffic across a network of independent nodes operated by participants worldwide. This decentralized setup ensures no single entity can track your complete browsing history. As Private Internet Access puts it:
"A dVPN distributes that control across multiple participants, shifting how trust is handled within the network."
With no central authority, individual nodes can't see both the origin and destination of your traffic. Multi-hop routing adds another layer of security by passing your data through at least three separate nodes, making it nearly impossible for any single node to trace your activity. This decentralized routing approach creates a foundation for transparency and security.
Transparency Through Blockchain
Traditional VPNs often claim they keep "no logs", but users have to trust these assertions without proof. Blockchain-based VPNs flip this model by using open-source code and transparent infrastructure that anyone can audit. Actions like node registration and performance ratings are recorded on an immutable blockchain ledger, offering verifiable evidence instead of relying on blind trust.
Transparency also plays a role in how nodes are evaluated. Blockchain platforms use publicly available data to assess node performance, enabling users to choose nodes with proven reliability. This approach has driven a surge in dVPN adoption, especially in areas with heavy internet censorship. While traditional VPN usage dropped by 15% in such regions, decentralized VPNs saw a 340% increase. The combination of technical transparency and economic incentives makes these platforms particularly appealing.
Financial Incentives for Privacy Protection
Blockchain-based VPNs use token-based economic models to reward node operators directly for maintaining privacy and uptime. Instead of paying a centralized company, users make payments through smart contracts to individual operators. This decentralized structure ensures that operators have a strong financial motivation to provide secure and reliable service.
Most dVPNs follow a usage-based pricing model, charging around $0.04 to $0.06 per GB. Payments are typically made with cryptocurrency, removing the need to share sensitive payment details with a central authority. This system not only enhances privacy but also keeps costs flexible - you pay only for what you use.
As Axis Intelligence explains:
"The decentralized nature of dVPNs means that even if one node is compromised, the encryption integrity remains intact".
This payment model, combined with the decentralized structure, ensures that operators remain incentivized to prioritize your privacy and security.
Privacy Comparison: Traditional VPNs vs Blockchain-Based VPNs
Comparison Table
Traditional VPNs rely on a single provider to manage and secure your data, while blockchain-based VPNs (dVPNs) spread that responsibility across a decentralized network. Here's how they stack up:
Feature | Traditional VPNs | Blockchain-Based VPNs (dVPNs) |
|---|---|---|
Network Structure | Centralized servers managed by one company | Peer-to-peer network of independent nodes |
Logging Policy | "No-logs" claims (difficult to verify) | Decentralized design prevents logging |
Anonymity | Limited (requires personal details) | High (Web3 wallet only, no personal data) |
Routing Method | Single-hop | Multi-hop (typically 3–6 hops) |
Censorship Resistance | Moderate (vulnerable to blacklisting) | High (uses residential IPs and global nodes) |
Node Trust | Relies on a single provider | Trust distributed across multiple nodes |
Metadata Protection | Provider sees both source and destination | No single node sees the full path |
Breaking Down Key Features
Logging Policy: Traditional VPNs often advertise "no-logs" policies, but verifying these claims is tricky. Blockchain-based VPNs, on the other hand, are built to avoid centralized logging altogether. Temporary session keys and the decentralized network structure ensure that no single entity can track your activity.
Anonymity: Using traditional VPNs usually means sharing personal information, such as an email address or billing details. In contrast, dVPNs only require a Web3 wallet for payments, keeping your personal identity completely out of the picture.
Metadata Protection: Even encrypted traffic can reveal metadata, like who you're communicating with or when. Blockchain-based VPNs address this by using multi-hop routing, splitting your traffic across multiple nodes so no single participant can see the entire data path.
What the Comparison Shows
This comparison highlights a critical privacy gap: Traditional VPNs can see everything about your online activity, from your IP address to the websites you visit. Using them means placing full trust in the provider to handle your data responsibly.
Blockchain-based VPNs eliminate this need for trust. By routing your data through multiple global nodes (3–6 hops), they ensure that no single node has a complete view of your activity. Some dVPNs even take it further with mixnets, which scramble encrypted data from multiple users, making it nearly impossible to trace traffic back to an individual.
The pricing model of dVPNs adds another layer of privacy. Instead of a subscription tied to your credit card, you pay for what you use - typically $0.04 to $0.06 per GB - via cryptocurrency. This approach avoids recurring payments and keeps your financial details private.
For users handling sensitive information or working in high-risk situations, the decentralized approach offers stronger privacy safeguards. Instead of relying on a provider's promises, you gain protection from a system designed to make tracking and logging virtually impossible.
MASQ VPN Network: Blockchain Privacy in Practice
Decentralized Peer-to-Peer Network
The MASQ Network operates without relying on central servers or a single governing authority. Since its launch in 2019, it has been built on a decentralized peer-to-peer protocol powered by a global network of community-operated nodes.
When you connect to MASQ VPN, your internet traffic is routed through multiple nodes spread across the globe. This design ensures no single node can see both the origin and destination of your data, making it impossible for any node to piece together your full data path. This setup is a key element in MASQ's approach to censorship resistance, which we'll explore further.
Global Traffic Routing and Censorship Resistance
MASQ's dynamic network offers strong protection against censorship. Unlike traditional systems that rely on fixed data centers, MASQ's network constantly adapts, making it difficult for blacklists to keep up. The routing is borderless, often passing through multiple countries, which shields your connection from regional monitoring. This ensures no single jurisdiction can track or control your internet access.
Integration with MASQ Ecosystem
MASQ VPN works seamlessly with the MASQ Browser and Timpi Search to create a comprehensive private internet experience. The MASQ Browser prioritizes privacy and supports decentralized Handshake domain resolution, while Timpi Search provides independent search results from one of the largest search indexes globally - not based on Google or Bing. Together, these tools form a unified private internet gateway, so you don’t need to juggle multiple services for online privacy.
MASQ offers basic features for free, with the option to upgrade to MASQ Premium starting at $8 per month. Premium users gain access to enhanced privacy features and an ad-free experience. Payments can be made using credit cards or cryptocurrency - no account setup required.
Conclusion: Privacy Through Blockchain-Based VPNs
Key Privacy Benefits of Blockchain
Blockchain-based VPNs tackle the trust issues that plague traditional VPNs by routing your traffic through multiple global nodes. This approach ensures that no single node has access to the full picture of your online activity. With no central servers to target, your data remains scattered and secure.
The multi-hop routing system adds another layer of protection, making it nearly impossible to trace your activity. Even if one node is compromised, the encryption remains intact, safeguarding your privacy. Contrast this with traditional VPNs - if their central servers are breached, all user data could be exposed.
Another game-changer is blockchain's transparency. Unlike traditional VPNs that operate behind closed doors, blockchain-based systems allow you to verify how the network operates. You don't have to rely on marketing promises when you can observe the protocol in action.
These features form the foundation of MASQ’s approach to delivering enhanced privacy for its users.
Why MASQ Leads in Online Privacy
MASQ takes these blockchain-powered privacy benefits and integrates them into a complete private internet solution. Its VPN network works seamlessly with the MASQ Browser and Timpi Search, creating a unified gateway where your data is neither tracked nor monetized.
MASQ’s commitment to decentralization drives this vision. The 2026 merger with Timpi brought one of the largest independent search indexes into the fold, completing an ecosystem where you remain in control of your data. Privacy here isn’t an add-on - it’s the default setting.
Starting at just $8 per month for Premium features, MASQ offers an accessible and effective solution for anyone prioritizing online privacy. No technical know-how is needed - just reliable, community-driven protection designed to keep you secure.
VPN vs dVPN Explained: Privacy, Security & The Future of Online Anonymity
FAQs
Do I need crypto to use a dVPN?
You don’t always need to use cryptocurrency to access a decentralized VPN (dVPN). While many dVPNs integrate crypto for handling micropayments or rewarding node operators, some offer the option to connect without involving digital currencies. In most cases, cryptocurrency is used for transactions or as incentives, but it’s not a mandatory part of enjoying the privacy and security features that dVPNs provide.
Can a dVPN still leak my IP or DNS?
A decentralized VPN (dVPN) like MASQ steps up your online privacy game by using encryption and multi-hop routing. This makes it tougher for anyone to track your IP or DNS activity. However, leaks can still happen, often due to weak spots in your device settings, operating system, or browser.
To keep yourself protected, it’s crucial to:
Configure your dVPN correctly.
Regularly update your software and devices.
Use leak protection tools to add an extra layer of security.
While MASQ’s decentralized setup and no-logging policy provide strong privacy safeguards, staying alert and proactive about your security is key.
What happens if a dVPN node is compromised?
If a dVPN node gets compromised, there’s a chance that traffic passing through it could be exposed, putting privacy or data at risk. But decentralized VPNs, like MASQ, address this concern effectively. They use multi-hop routing and strong encryption to safeguard user data. This means your traffic is encrypted multiple times and sent through several nodes, making it much harder to intercept or decipher.
While risks like metadata exposure or traffic correlation attempts can still exist, a network powered by the community and equipped with solid security measures significantly reduces these vulnerabilities, helping to keep user privacy intact.




