
AI-driven censorship is advancing, making it harder for traditional VPNs to bypass restrictions. Decentralized VPNs, like MASQ, offer a new solution by using peer-to-peer networks that are harder to detect and block. Unlike centralized VPNs that depend on fixed servers (vulnerable to shutdowns and legal pressures), decentralized systems rely on independent nodes, making them resilient against government crackdowns and AI traffic analysis. Key differences include:
Centralized VPNs: Use fixed servers, are prone to AI detection, and often require trust in "no-log" claims.
Decentralized VPNs: Operate through dynamic, serverless networks, making logging impossible and traffic harder to identify.
Decentralized VPNs also use advanced obfuscation techniques, like disguising traffic as regular HTTPS, to evade AI detection. While centralized VPNs may be faster and easier to set up, decentralized options prioritize privacy and censorship resistance, ensuring safer access to information in heavily monitored regions.
1. Traditional VPNs
Architectural Design
When comparing MASQ vs. traditional VPNs vs. Tor, it's clear that traditional VPNs rely on a hub-and-spoke model, with data centers acting as the central hub. This setup creates a single point of failure, making these systems vulnerable if authorities target their servers. A striking example occurred in April 2022 when India's Computer Emergency Response Team (CERT-In) mandated VPN providers to log user data for five years. This policy led several major providers to shut down their physical servers in India entirely.
Resistance to AI Traffic Analysis
AI-powered censorship systems have become a significant challenge for traditional VPNs. These systems analyze traffic patterns, even when encrypted, to detect VPN usage. Protocols like WireGuard and OpenVPN, though widely used, inadvertently expose metadata through features like magic headers and consistent byte patterns, making them susceptible to Deep Packet Inspection (DPI).
Elena Voss, a Senior Cybersecurity Analyst & Privacy Advocate, highlights the issue:
"Censors aren't just blocking IPs anymore; they're using AI to sniff out patterns in your encrypted data. Even if your data is scrambled, the shape of the traffic gives it away."
Mazay Banzaev, founder of Amnezia VPN, adds a forward-looking perspective:
"At the moment, it's almost impossible to use advanced machine learning algorithms to detect and block VPN traffic for widespread use because it's too expensive... but it will become cheaper over time".
By early 2026, these techniques had already enabled Russia to block nearly 200 VPN services, showing how effective AI-driven censorship can become.
Logging and Privacy Policies
Despite claims of maintaining no logs, many traditional VPNs operate on closed-source systems, which limits transparency and makes independent verification difficult. Brien, CEO of URNetwork, emphasizes this skepticism:
"When someone says no logs, the right response is: show me the schema and server code."
Moreover, centralized VPN providers are particularly vulnerable to legal pressures. In regions like the "Five Eyes" alliance, strict data retention laws can force providers to hand over sensitive user information, including billing details, email addresses, and connection logs.
Censorship Circumvention
Traditional VPNs were originally designed with security in mind, not to bypass censorship. This design limitation becomes apparent when facing modern, AI-driven national firewalls. Governments can blacklist server IPs, hijack DNS requests, or even seize physical hardware to disrupt VPN services.
For instance, in March 2024, Russia introduced a law criminalizing the distribution of information about censorship circumvention. This led to the removal of many VPN apps from the Apple App Store. The centralized nature of these services leaves them particularly exposed to such crackdowns, as a single government action can disrupt all servers operated by a provider.
Up next, we’ll explore how decentralized VPNs tackle these vulnerabilities and offer a different approach to privacy and censorship resistance.
2. Decentralized VPNs (e.g., MASQ VPN Network)
Architectural Design
Decentralized VPNs take a different approach compared to traditional ones. Instead of routing traffic through centralized servers, they rely on a peer-to-peer (P2P) mesh network where data flows between independent nodes. This setup removes the single point of failure that often makes conventional VPNs vulnerable to censorship and surveillance.
The MASQ VPN Network is a great example of this model. Since 2019, it has been using a decentralized P2P protocol to route traffic without any central authority or logging. If one node is blocked, the system automatically redirects traffic through another node, making it almost impossible for censors to shut down the entire network. This serverless design operates across several layers: the physical mesh layer (P2P connections), the routing layer (using techniques like onion routing or mixnets), and the economic layer (where node operators are incentivized through tokens). This layered approach also supports advanced obfuscation methods, making it harder for AI systems to analyze and identify traffic patterns.
Resistance to AI Traffic Analysis
AI-powered censorship tools don’t always need to see the content of your data - they can analyze metadata to detect VPN usage. Decentralized VPNs combat this by using obfuscation techniques that make VPN traffic look like regular HTTPS or random UDP data. Advanced networks go further by employing mixnets, which split data into packets, encrypt them with multiple layers (like Sphinx encryption), and route them through several independent nodes - usually five - so no single node knows the full path. Some even use WebRTC to embed data in what looks like normal video call traffic, creating "noise" that AI tools struggle to interpret.
By constantly shifting traffic across a large number of independent nodes, decentralized systems make it far harder for AI to spot patterns compared to the predictable infrastructure of centralized VPNs.
Logging and Privacy Policies
A key advantage of decentralized VPNs is their serverless design, which makes logging technically impossible. There’s no central database to store user logs, no company that can be forced to release data, and no physical infrastructure that can be targeted.
As Kade from Onchain Magazine puts it:
"Decentralized VPNs bring privacy and trustlessness to the VPN ecosystem. You need not trust a DPN to handle your data with caution; thanks to a DPN's serverless design, your data cannot be stored by default".
MASQ’s system reflects this principle. Without central logging, even if authorities demand user data, there’s nothing to hand over. This stands in stark contrast to traditional VPNs based in "Five Eyes" countries (USA, UK, New Zealand, Australia, Canada), where data-sharing agreements enable mass surveillance.
Censorship Circumvention
Decentralized VPNs are much harder to block. Their distributed nature means censors would need to identify and blacklist an enormous number of constantly changing peer IP addresses - a nearly impossible task. If one route is blocked, the network simply finds another path through different nodes.
With around 1.6 billion people (31% of internet users) now relying on VPNs, and AI-driven censorship becoming more sophisticated, decentralized systems offer a critical way to maintain unrestricted internet access. Their ability to adapt and reroute ensures they remain a powerful tool against censorship.
Why VPNs are scams and what to do about it by Harry Halpin | Devcon SEA
Strengths and Weaknesses
Traditional vs Decentralized VPNs: Key Differences in Privacy and Censorship Resistance
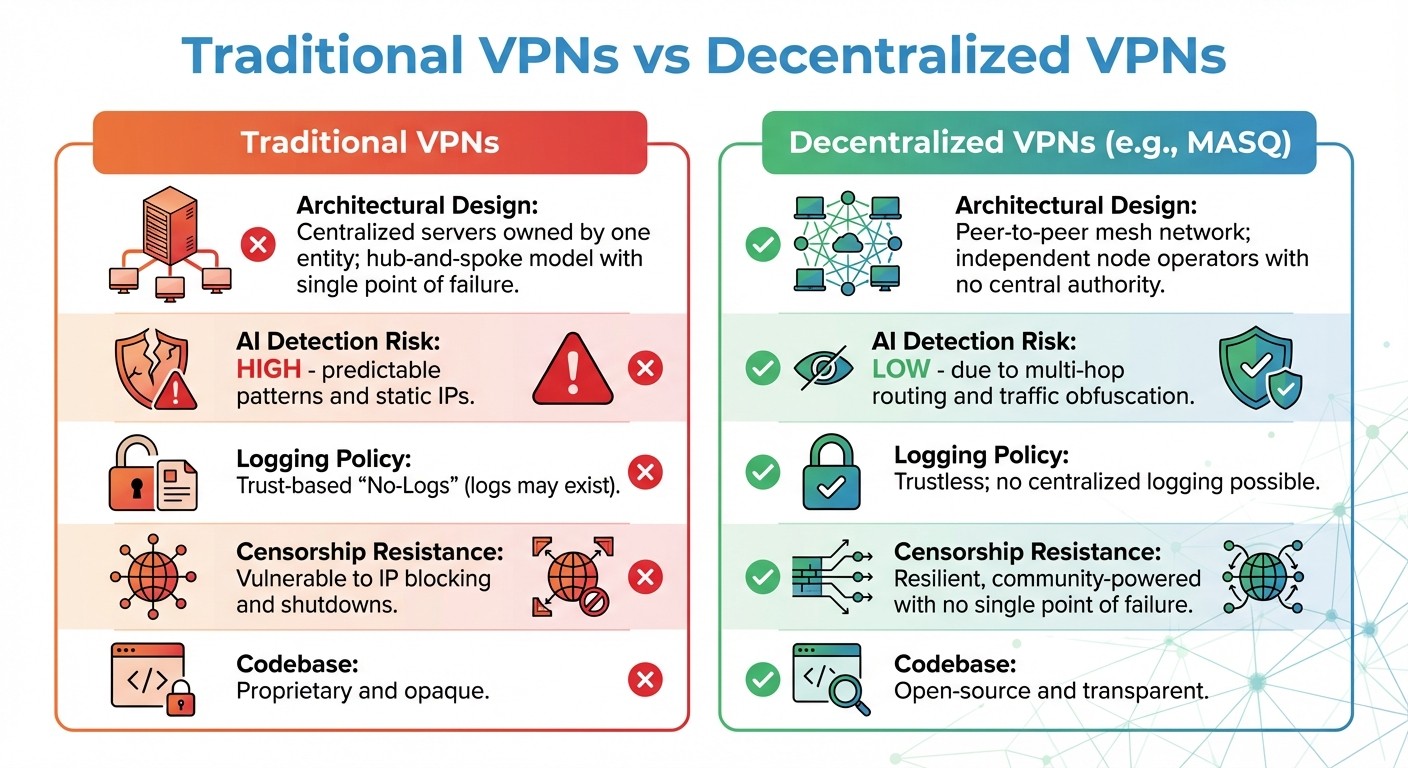
Traditional VPNs and decentralized systems differ in their core principles, leading to unique advantages and vulnerabilities, especially when dealing with AI-driven censorship.
Decentralized VPNs flip the script. Unlike traditional VPNs, they don’t rely on centralized logging - there’s no central database to attack, and no single company that governments can pressure. Casey Ford, PhD, Communications Lead at Nym, highlights this issue:
"Traditional VPNs are largely marketed on false promises. Most VPNs are not actually private at all, and one key reason for this is that they are centralized and this centralization poses major privacy risks".
Here’s a breakdown of how the two systems stack up:
Feature | Traditional VPNs | Decentralized VPNs (e.g., MASQ) |
|---|---|---|
Architectural Design | Centralized servers owned by one entity; hub-and-spoke model with single point of failure | Peer-to-peer mesh network; independent node operators with no central authority |
AI Detection Risk | High; predictable patterns and static IPs | Low, due to multi-hop routing and traffic obfuscation |
Logging Policy | Trust-based "No-Logs" (logs may exist) | Trustless; no centralized logging possible |
Censorship Resistance | Vulnerable to IP blocking and shutdowns | Resilient, community-powered with no single point of failure |
Codebase | Proprietary and opaque | Open-source and transparent |
This comparison highlights how decentralized systems hold a distinct edge in combating modern censorship tools.
Decentralized networks make it nearly impossible for censors to keep up. Blocking such systems would require identifying and blacklisting thousands of ever-changing peer IP addresses. Even if one route gets blocked, the network quickly reroutes through other nodes. However, the trade-off is worth noting: traditional VPNs often deliver faster speeds and easier setup because they control their infrastructure. On the other hand, decentralized systems focus on privacy and censorship resistance, with blockchain-based token incentives ensuring better uptime and reliability across their node networks.
Conclusion
Decentralized VPNs stand out as a powerful solution against AI-driven censorship, surpassing traditional VPNs in resilience and adaptability. Their distributed structure eliminates the single points of failure that centralized systems often face, offering protection against government crackdowns, IP blacklisting, and forced shutdowns.
These systems leverage advanced techniques like obfuscation and multi-node routing to outsmart AI surveillance. As AI increasingly targets patterns in standard VPN protocols, decentralized networks fight back by adding randomized noise, disguising traffic as regular HTTPS, and routing data through multiple independent nodes. Mazay Banzaev, founder of Amnezia VPN, highlights this challenge:
"DPI is a technology that allows one to recognize what is inside the traffic... they are incorporating AI - obviously".
This evolving landscape renders static defenses less effective over time.
For users in regions with heavy surveillance, decentralized options like MASQ offer a lifeline. MASQ's peer-to-peer VPN network ensures uninterrupted access by dynamically rerouting traffic through alternative nodes when one path is blocked. This flexibility provides a robust shield against even the most aggressive government censorship efforts.
With around 1.6 billion people - roughly 31% of internet users - relying on VPNs for privacy, the stakes are high. As governments refine their AI-powered censorship tools, the shift from traditional VPNs, which depend on trust, to decentralized systems like MASQ, which enforce privacy through design, marks a pivotal change. This architectural approach to anonymity is shaping the future of unrestricted internet access.
FAQs
How can AI detect VPNs if my traffic is encrypted?
AI has the ability to identify VPN usage, even when traffic is encrypted, by examining indirect clues such as IP address reputation, connection patterns, and behavioral anomalies. Instead of analyzing the encrypted data itself, these techniques rely on metadata and the unique characteristics of the traffic.
Why are decentralized VPNs harder to block than traditional VPNs?
Decentralized VPNs are much harder to block since they don’t depend on centralized servers that can be easily targeted or shut down. Instead, they operate through a distributed network of user-run nodes, which makes it nearly impossible for censors to block every access point. On top of that, many decentralized VPNs use peer-to-peer protocols to disguise traffic patterns. This helps them evade AI-driven censorship systems by avoiding the predictable behaviors typical of centralized setups.
What are the trade-offs of using a decentralized VPN for everyday browsing?
Decentralized VPNs offer a significant boost to privacy and censorship resistance by skipping centralized servers entirely. This approach makes them harder to target for logging, throttling, or even seizure. Instead of relying on a single control point, they route traffic across a global network, which provides robust protection against surveillance.
That said, the peer-to-peer setup of decentralized VPNs can sometimes lead to slower speeds and less consistent reliability. Connection stability might fluctuate, and technical issues like network partitioning can occasionally crop up, impacting the overall user experience.




