
Decentralized VPNs (dVPNs) are reshaping online privacy by eliminating the vulnerabilities of centralized systems. Unlike traditional VPNs, which store user data in single locations, dVPNs distribute traffic across independent nodes, reducing risks like data breaches and credential theft. Here's why they matter:
No Single Point of Failure: Traffic is spread across multiple nodes, making it harder for attackers to target one location.
Enhanced Encryption: End-to-end encryption (e.g., AES-256) ensures data remains unreadable during transmission.
Multi-Hop Routing: Traffic passes through multiple nodes, hiding both origin and destination.
No Centralized Storage: Credentials are managed with public-key cryptography, not stored in vulnerable databases.
Zero-Knowledge Proofs: Users verify access rights without sharing personal details.
These features make dVPNs an effective tool for securing credentials, bypassing censorship, and protecting privacy during everyday online activities. Whether you're accessing sensitive systems or conducting Web3 transactions, dVPNs provide a safer alternative to traditional VPNs.
Risks of Centralized Credential Storage
How Centralized Systems Store Credentials
Centralized platforms manage login credentials by storing them in single databases or server clusters. This setup creates what security professionals often refer to as a "honeypot" - a highly attractive target for hackers and surveillance agencies due to the concentration of sensitive information in one location.
But the risks go deeper than just where passwords are stored. Many desktop and browser-based password managers leave plaintext passwords exposed in system memory. This vulnerability, identified as CWE-316 ("Cleartext Storage of Sensitive Information in Memory"), means that passwords remain accessible in RAM while the application is running. Even centralized VPNs vs. decentralized alternatives face similar issues - 33% of them leak user credentials into system memory.
Additionally, centralized providers have the capability to log session details, connection metadata, and browsing activity. Even when companies claim to follow "no-logs" policies, such assurances are difficult to verify. In cases of infrastructure breaches or legal demands, logs containing sensitive data - like your real IP address and usage patterns - can be exposed, leaving users vulnerable to ongoing risks.
These practices make centralized storage systems especially susceptible to large-scale breaches.
Consequences of Major Data Breaches
When centralized systems are breached, the fallout can be devastating. Recent vulnerabilities in centralized gateways such as Ivanti, Citrix, and Fortinet highlight this danger. Exploits like CVE-2025-0282, CVE-2025-22457, CVE-2023-3519, and CVE-2023-27997 allowed attackers to execute remote code without authentication. A single breach in these systems can compromise thousands of users at once.
Once attackers gain access to breached credentials, they can impersonate users and escalate their privileges. This access also enables them to launch highly convincing social engineering attacks, leveraging contextual information like device behavior. With 79% of Americans expressing concerns about their online privacy, such breaches not only erode trust but also leave users exposed to long-term risks far beyond the initial incident.
These vulnerabilities highlight the importance of decentralized VPNs, which distribute data across independent nodes using multi-hop technology, offering a more secure alternative to centralized systems.
How Decentralized VPNs Protect Your Credentials
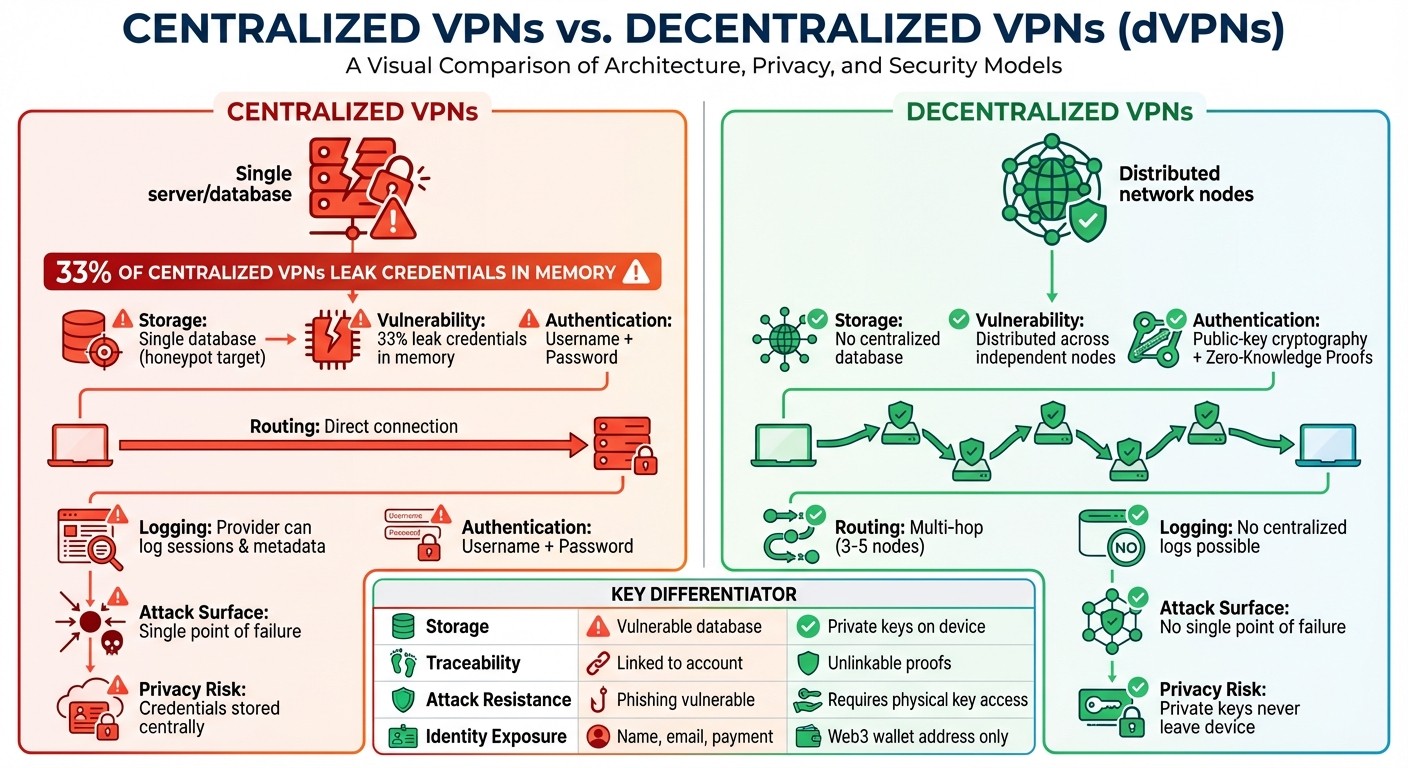
Centralized vs Decentralized VPN Security Architecture Comparison
Decentralized VPNs offer a fresh approach to safeguarding your credentials. Instead of relying on a single provider's centralized servers, they spread security across independent nodes. This eliminates centralized targets that often attract hackers. By combining encryption, cryptographic authentication, and other techniques, decentralized VPNs create a robust shield for your data. Let’s dive into how encryption and routing methods contribute to this protection.
End-to-End Encryption for Data Transmission
When you input credentials on a website, end-to-end encryption (E2EE) ensures that your data is transformed into unreadable ciphertext before leaving your device. Only the intended recipient - like the website you're accessing - can decrypt and read the information. This creates a secure pathway that blocks Man-in-the-Middle attacks, where hackers might try to intercept your data during transmission.
One widely used encryption standard, AES-256, employs 256-bit keys, making it nearly impossible to crack through brute force attempts.
"VPN encryption is critical in reducing the risk of having your data compromised when it is traveling over the internet by encoding the data packets."
– Becky McCarty, Linford & Co
Protocols such as WireGuard, OpenVPN, and Perfect Forward Secrecy add another layer of security. Even if encryption keys are compromised in the future, these protocols ensure that past sessions remain protected.
Multi-Hop Routing for Privacy Protection
Multi-hop routing takes privacy to the next level by spreading your traffic across multiple independent nodes. In a typical three-hop setup, the entry node knows your IP address but not your online activity, while the exit node can see your activity but has no clue about your identity. This setup effectively hides both the origin and destination of your data. Even if an exit node acts maliciously, it cannot trace your traffic back to your IP address.
Take MASQ, for example. This decentralized VPN platform uses separate nodes for the return path, making it harder for anyone to track traffic patterns or intercept credentials. MASQ also disguises data packets to resemble standard HTTPS traffic, further thwarting packet sniffing and traffic analysis.
"The 'MASQ' 3-hop route is the default minimum recommended route length for untraceable traffic across the MASQ Network."
– MASQ
Another layer of protection comes from MASQ’s "neighborhood" approach. Each node only interacts with up to five nearby nodes, preventing any single participant from mapping the entire network or tracing routing paths.
Avoiding Centralized Storage Vulnerabilities
Decentralized VPNs also address the risks tied to centralized storage. Traditional systems often store user credentials in central databases, which are prime targets for breaches or legal subpoenas. Decentralized VPNs eliminate this risk entirely.
Instead of the usual username and password setup, these VPNs use public-key cryptography. For instance, MASQ users sign requests with a private key to verify their identity and manage bandwidth payments - all without revealing personal information. Your identity is linked to a Web3 wallet address rather than personal details like your name, email, or phone number. Moreover, payment wallets are not connected to your IP address, ensuring anonymity.
An automated "Accountant Module" tracks peer-to-peer transactions locally on each node, avoiding the need for a central billing system. Some advanced systems even use mixnets, which fragment data so thoroughly that reconstructing your online activity becomes mathematically impossible for any observer.
Cryptographic Authentication and Zero-Knowledge Proofs
Decentralized VPNs take security up a notch by combining encryption and multi-hop routing with cryptographic authentication methods. This approach ensures that your credentials remain secure, even in the face of phishing attempts or credential-based attacks.
Private Key Authentication Instead of Passwords
Instead of relying on traditional passwords, decentralized VPNs use public-key cryptography. Here, a private key stored on your device acts as a digital signature. When you connect to the network, your device uses this private key to sign requests, proving you're authorized to use the service.
Take MASQ as an example: the originating node signs the peer node's public key using its consuming wallet's private key. This signature confirms your authorization and demonstrates available funds - without ever exposing the private key itself. As MASQ Network explains:
This process proves that the originating Node knows the private key of its consuming wallet so it can pay for its own requests!
This method eliminates common vulnerabilities. Phishing becomes irrelevant because there’s no password to steal, and credential stuffing is ineffective since the private key never leaves your device or gets stored in a central database. By integrating cryptographic authentication with existing encryption techniques, decentralized VPNs close the door on many traditional security flaws.
Feature | Traditional Password Authentication | Cryptographic/ZKP Authentication |
|---|---|---|
Storage | Centralized database vulnerable to breaches | Private keys remain on the user's device |
Visibility | Password or hash sent to a server | Sensitive attributes are not publicly exposed |
Traceability | Sessions easily linked to a specific account | Unlinkable and rerandomizable proofs |
Attack Resistance | Vulnerable to phishing and credential stuffing | Resistant; requires access to the physical private key |
Zero-Knowledge Proofs for Identity Verification
Zero-knowledge proofs (ZKPs) elevate privacy by allowing you to verify your access rights - like proving you've paid for bandwidth - without sharing personal details like your identity, location, or browsing activity.
For instance, in January 2026, the Nym network introduced "zk-nym" credentials. Users receive partially blinded signatures from a NymAPI Quorum, which are aggregated into a "ticketbook" on their devices. When accessing the mixnet, they use these credentials to prove bandwidth payment to an ingress gateway. Crucially, this process doesn’t reveal their blockchain address or link payment to browsing behavior. The rerandomizable nature of these credentials ensures that each use appears unique, further protecting user privacy.
As Nym's documentation explains:
These keys are used as private attribute values within generated credentials which are verified via zero-knowledge and not publicly exposed.
Practical Uses for Decentralized VPNs
Accessing Geo-Blocked or Censored Content
Decentralized VPNs offer a clever way to bypass geo-restrictions and censorship without compromising your credentials. Unlike traditional VPNs that often rely on easily identifiable data center IP addresses, dVPNs route your traffic through residential nodes. This makes your connection blend seamlessly with regular internet traffic, making it much harder for censors to block access without disrupting everyday online activity.
The multi-hop design of dVPNs adds another layer of security. Your traffic doesn’t travel directly from point A to point B; instead, it bounces through 1–5 independent nodes. This setup ensures no single node can see both your origin and destination, significantly reducing the risk of tracking or credential exposure. Additionally, dVPNs use protocol obfuscation techniques to mimic standard HTTPS traffic, helping them evade deep packet inspection (DPI).
Before diving into sensitive content, it’s smart to test for leaks using tools like ipleak.net or dnsleaktest.com to ensure your real IP address isn’t exposed. For tasks like streaming, where speed is a priority, stick to 1–2 hops. But if you’re trying to bypass strict censorship, go for 3–5 hops to enhance your anonymity. Pairing your dVPN with DNS-over-HTTPS (DoH) or DNS-over-TLS (DoT) is another step to ensure your DNS queries stay private.
This strong privacy framework is also crucial when handling digital transactions.
Securing Web3 Transactions
Web3 transactions demand more than just encryption for security. MASQ, for instance, integrates private key authentication to safeguard blockchain transactions against credential theft.
To keep your private keys secure, store them in hardware wallets like Ledger or Trezor, even when using a dVPN. For high-value transactions, consider using multi-signature wallets, which require multiple private keys for authorization. Always double-check recipient addresses and smart contract actions before signing any transaction. If you’re exploring new DeFi protocols, reviewing their security audits can help you identify potential vulnerabilities.
Beyond content access and blockchain security, dVPNs are also effective for everyday online protection.
Protecting Credentials During Daily Activities
Everyday online activities like banking, shopping, or working remotely can expose your credentials to risks. Decentralized VPNs address this by eliminating single points of failure. Their distributed architecture ensures no single entity can log your activity. Features like ephemeral session keys and bandwidth receipts also prevent metadata from being used to reconstruct your online identity.
To further safeguard your activities, enable a kill switch and lock your DNS settings to prevent leaks in case your connection drops. For high-value tasks like banking or Web3 transactions, using at least a 3-hop route enhances anonymity and protects your metadata. Additionally, MASQ’s token-based, pay-as-you-go model eliminates the need for credit card subscriptions, removing another layer of identity exposure tied to traditional payment methods.
Conclusion
Centralized storage systems have long been vulnerable to breaches, but decentralized VPNs are changing how credentials are protected. MASQ achieves this by replacing centralized servers with a peer-to-peer mesh network of independent nodes. This setup eliminates single points of failure, ensuring your data moves securely through multiple nodes. With onion-style encryption and cryptographic authentication using private keys, no single entity can trace your activity or exploit centralized database vulnerabilities.
MASQ's 3-hop routing makes traffic untraceable, and its clandestine routing techniques disguise data to bypass deep packet inspection. The distributed nature of the network means no centralized logs exist, and traffic is automatically rerouted if nodes go offline, maintaining uninterrupted privacy.
"The MASQ Network, once live, will grow to a point where it cannot be shutdown. No large entity or Government could censor the network from allowing users to access the freedom of the entire Internet."
Additionally, MASQ's token-based payment system removes the need to connect credit cards or personal payment details to your online activity. Whether you're bypassing censorship, securing Web3 transactions, or simply browsing, decentralized VPNs offer a level of privacy and security that centralized systems cannot achieve. Your credentials remain strictly yours - safeguarded by strong encryption, distributed across independent nodes, and authenticated without the risks of password-based databases.
This architecture paves the way for a new standard in online privacy and security.
FAQs
What makes decentralized VPNs more secure than traditional VPNs?
Decentralized VPNs, or dVPNs, take a different approach to online security by using a peer-to-peer network made up of distributed nodes. Unlike traditional VPNs that depend on centralized servers, dVPNs remove the risk of a single point of failure. This reduces the chances of data breaches and unauthorized access.
Another key advantage is that dVPNs don’t keep user logs, offering a higher level of privacy and anonymity. Their decentralized design also makes them harder to censor, enabling users to bypass restrictions and browse the internet with more freedom and security.
How does multi-hop routing improve privacy in decentralized VPNs?
Multi-hop routing adds an extra shield of privacy to decentralized VPNs by encrypting your data as it passes through multiple nodes before reaching its final destination. Each node in the chain applies another layer of encryption, making it significantly harder for anyone to trace your online activity back to you. This layered approach offers a higher level of anonymity compared to single-hop routing, which relies on just one server to handle your data.
Decentralized VPNs like MASQ take this concept even further. Their unique network design focuses on enhancing privacy and resisting censorship. By channeling your traffic through several nodes, these VPNs make it nearly impossible for external parties to monitor your activities or access sensitive information. On top of protecting your data, this method helps you bypass geo-blocks and censorship, giving you the freedom to browse securely and without restrictions.
How do decentralized VPNs use public-key cryptography to safeguard my credentials?
Decentralized VPNs rely on public-key cryptography to protect your credentials. This method encrypts your data using a unique key, ensuring that only the intended recipient can decrypt and access it. As a result, your information remains secure from hackers or unauthorized access.
By adding multiple layers of encryption, decentralized VPNs provide an additional layer of defense. This makes it extremely difficult for attackers to intercept or steal your data while you're online. Such robust security measures are crucial for safeguarding sensitive information in an increasingly digital world.




