
Deep Packet Inspection (DPI) is a method that examines the actual content of internet data packets, not just their metadata like IP addresses. While it helps with cybersecurity, network management, and legal compliance, it raises serious concerns about privacy, censorship, and net neutrality. Here's the debate:
Pros: Improves cybersecurity by detecting threats, enhances network performance, and aids in legal compliance for industries like healthcare and finance.
Cons: Violates privacy by exposing sensitive data, undermines net neutrality by enabling selective traffic control, and enables censorship and surveillance by governments and corporations.
Globally, DPI's legal use varies:
Permitted: U.S. (regulated for surveillance and network management).
Restricted: EU (strict privacy laws limit its use).
Exploited: China, Russia, and others use it for censorship and control.
Decentralized tools, like MASQ, offer solutions to protect privacy by routing traffic through peer-to-peer networks, making it harder for DPI to monitor or block data. The debate continues: should the benefits of DPI outweigh its risks to freedom and privacy?
How your employer sniffs you, or Deep Packet Inspection.
What Is Deep Packet Inspection and Why Does It Matter?
Deep Packet Inspection (DPI) is a sophisticated network filtering technique that goes beyond examining just the metadata, like IP addresses or port numbers, found in data packet headers. Instead, it analyzes the actual content - known as the "payload" - of these packets as they move through a network checkpoint. This deeper level of scrutiny allows for a more detailed understanding of the data being transmitted, distinguishing DPI from basic packet inspection methods that only skim the surface of information like addresses and protocols.
How DPI Works
To understand DPI's importance, it's helpful to look at how it functions. Traditional packet inspection operates on the Network (Layer 3) and Transport (Layer 4) levels of the OSI model, focusing on basic details like IP addresses, port numbers, and protocol types. DPI, however, delves into the Application Layer (Layer 7), where it can identify specific applications - such as BitTorrent, Tor, or encrypted messaging apps - and even examine the content within those applications.
DPI achieves this by using signature matching and heuristic analysis, relying on a database of protocol behaviors and patterns to recognize and classify data. In some cases, it even decrypts or decompresses data to analyze encrypted traffic. Advanced DPI systems, like those powered by Narus technology, can process data at speeds of up to 10 gigabits per second. To inspect data, network operators often use methods like port mirroring or network taps to duplicate traffic streams. Once captured, DPI systems scrutinize a wide range of data types, including HTTP search queries, DNS responses, VoIP calls, and email content. This capability highlights DPI's utility in managing networks but also raises ethical concerns about potential misuse.
Common Uses of DPI
DPI serves a variety of purposes, including:
Cybersecurity: It identifies and blocks malware, intrusions, and other cyber threats.
Network Management: It helps ensure Quality of Service (QoS) by prioritizing time-sensitive traffic, like video calls, over less critical data.
Compliance and Monitoring: Organizations use it to prevent data breaches by detecting and stopping unauthorized transfers of sensitive information.
However, DPI's capabilities can also be used for more intrusive purposes. For instance, in April 2017, Egypt's National Telecom Regulatory Authority used DPI to block encrypted messaging and VoIP services, including Signal, FaceTime, and WhatsApp calls. While these applications demonstrate DPI's practical uses, they also highlight the ethical dilemmas it creates.
The Ethical Conflict
The power of DPI brings with it a host of ethical challenges. While it plays a crucial role in bolstering network security and efficiency, it can also be employed for invasive surveillance, censorship, and actions that undermine net neutrality. Jeff Chester, Executive Director of the Center for Digital Democracy, explains the potential for abuse:
"DPI allows service providers to 'readily know the packets of information you are receiving online - from e-mail, to websites, to sharing of music, video and software downloads.'"
This duality sparks debate: Do the benefits of DPI, such as improved security and better network management, outweigh its risks to privacy, freedom of expression, and the principle of a fair and open Internet?
Feature | Conventional Inspection | Deep Packet Inspection (DPI) |
|---|---|---|
OSI Layers | Layers 3 & 4 (Network/Transport) | Layers 3 through 7 (Application) |
Focus | Packet Headers (IP, Port, Protocol) | Packet Payload (Actual Content) |
Visibility | "Cover of the book" | "Full text of the book" |
Security Use | Basic Firewalling, NAT | Malware detection, Intrusion prevention |
Privacy Risk | Low (Metadata only) | High (Content surveillance) |
Network Use | Routing and switching | Traffic shaping, QoS, Censorship |
Arguments for Legalizing Deep Packet Inspection
Despite privacy concerns, many experts argue that the practical benefits of Deep Packet Inspection (DPI) justify its legal use. Advocates often point to three main advantages: better cybersecurity, more efficient network management, and compliance with legal and regulatory frameworks. These benefits highlight how DPI can serve purposes beyond mere surveillance.
Strengthening Cybersecurity
DPI goes beyond basic packet headers, examining the actual content of data packets to uncover threats that traditional firewalls or standard VPNs might miss. Conventional firewalls may fail to detect attacks hidden within legitimate-looking traffic or distributed across multiple packets. DPI operates at the application layer, providing the visibility needed to detect threats like buffer overflow attacks, intrusions, and viruses.
It also supports Data Loss Prevention (DLP) by stopping unauthorized outbound data transfers. This is critical for organizations dealing with sensitive information, as it helps prevent both accidental leaks and deliberate theft. DPI also enhances network resilience by filtering malicious traffic in real time, protecting against Denial-of-Service attacks.
Improving Network Management
DPI isn't just about security - it also optimizes network performance. By identifying specific applications like Zoom, BitTorrent, or email clients at the application layer, DPI allows organizations to manage high-bandwidth, non-essential traffic that could otherwise slow down the network.
It helps ensure Quality of Service (QoS) by prioritizing time-sensitive applications, such as VoIP and video conferencing, over less critical traffic. Additionally, DPI provides statistical insights into usage patterns, enabling administrators to plan for future capacity needs and customize service plans based on actual application usage.
Meeting Legal and Regulatory Requirements
In industries like healthcare and finance, DPI plays a crucial role in ensuring compliance with strict legal standards. Organizations must prevent unauthorized transmissions of sensitive information - such as patient records or financial data - and DPI offers a technical solution by inspecting outbound traffic.
Another important use is lawful interception. In 2006, the FCC adopted Title 47, Subpart Z, requiring Internet Service Providers to comply with the CALEA (Communications Assistance for Law Enforcement Act). According to Wikipedia, "DPI was one of the platforms essential to meeting this requirement and has been deployed for this purpose throughout the U.S.". This law ensures that telecommunications carriers can support real-time forensics for court-ordered surveillance, reinforcing DPI's role as a tool for law enforcement when used under proper legal authority.
Arguments Against Legalizing Deep Packet Inspection
While Deep Packet Inspection (DPI) offers certain practical advantages, its potential for misuse raises serious ethical concerns. The technology's ability to delve into the actual content of internet traffic - not just metadata - sparks debates about privacy, fairness, and online freedoms.
Privacy Violations
DPI's capability to inspect packet payloads exposes sensitive personal information that traditional methods would typically leave untouched. This includes browsing history, search queries, and even private conversations. Technology writer Muhammad Raza highlights the risks:
"Lawful inspection at this layer may involve decrypting payload data - a process that can resemble a Man-in-the-Middle (MITM) intervention if the data was encrypted at source"
. This means that even encrypted communications might not be entirely safe from scrutiny. By allowing Internet Service Providers (ISPs) to examine and even modify content, DPI challenges the Internet's original end-to-end design principles.
Threats to Net Neutrality
DPI gives ISPs the ability to analyze and manipulate traffic based on its content or application, which undermines net neutrality - the principle that all internet traffic should be treated equally. For instance, DPI can be used to prioritize certain services, like paid streaming platforms, while throttling others, such as peer-to-peer file sharing. By turning packet inspection into a tool for selective traffic management, ISPs disrupt the Internet's foundational principle of equal access. This could result in a fragmented online experience where commercial or political motives dictate what users can access.
Enabling Censorship and Surveillance
DPI also serves as a powerful tool for censorship and surveillance, allowing governments and corporations to filter and monitor online activity. It can block privacy-focused tools like TOR or peer-to-peer applications such as BitTorrent, limiting how users share and access information. Moreover, DPI can restrict access to specific websites, extract search queries, and monitor DNS transactions. Since DPI is often implemented at ISP gateways or by cloud providers, its reach can extend to entire regions or populations, enabling sweeping policy enforcement that affects millions of users at once.
Legal Status of DPI: A Global Comparison
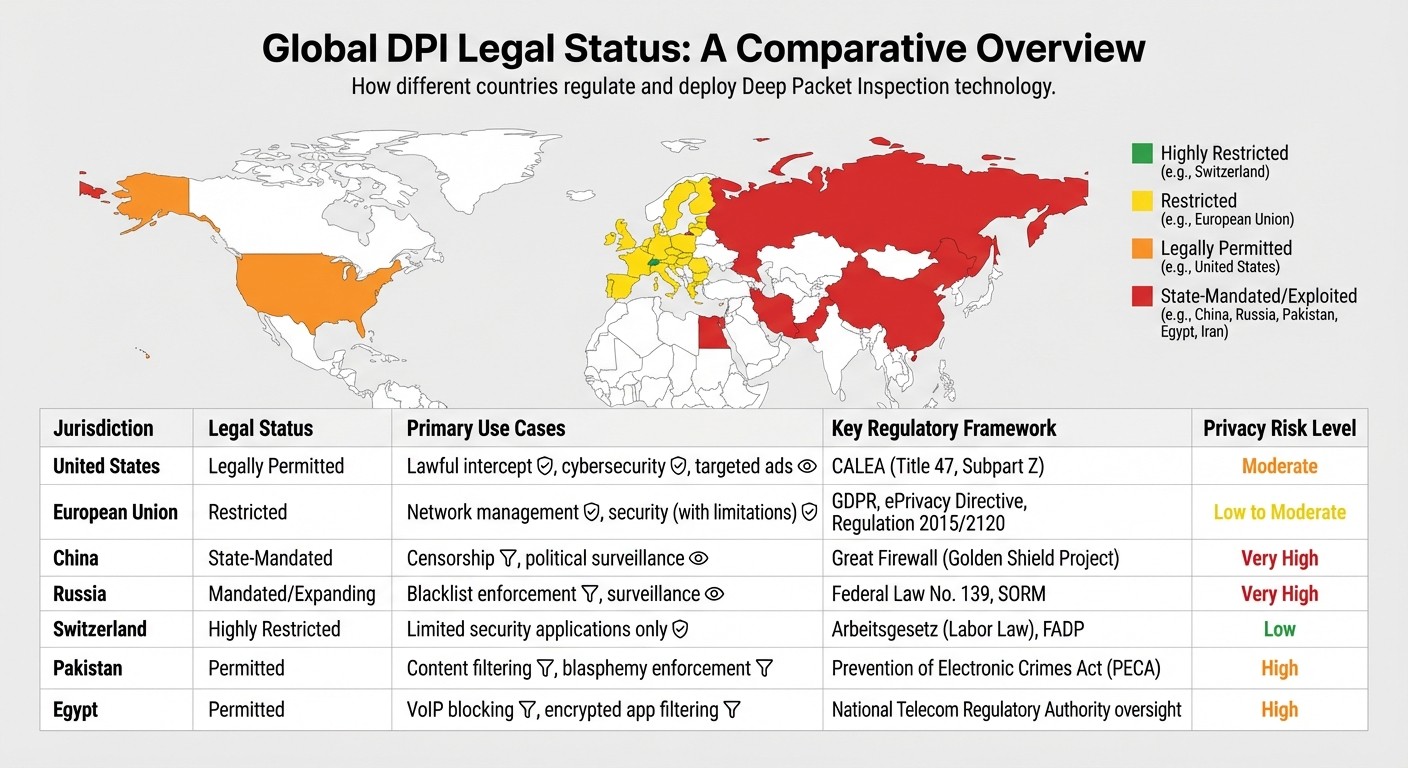
Global Deep Packet Inspection Legal Status and Privacy Risk Comparison
The rules governing Deep Packet Inspection (DPI) vary widely across the world. Some countries require DPI for government surveillance, while others tightly regulate or limit its use to protect privacy. These differences show how governments weigh security concerns against individual freedoms.
Where DPI Is Legally Permitted
In the United States, DPI is allowed under the Communications Assistance for Law Enforcement Act (CALEA). Title 47, Subpart Z mandates that telecommunications and internet service providers maintain DPI capabilities for court-approved surveillance. This law ensures that law enforcement can use DPI with proper legal authorization. Beyond surveillance, U.S. ISPs also use DPI for network management, cybersecurity efforts, and even targeted advertising under specific legal frameworks.
The European Union takes a stricter stance. While DPI is permitted for addressing certain security threats or managing networks, it is highly regulated under GDPR and the ePrivacy Directive. European Directive 2000/31/EC explicitly prohibits ISPs from being required to monitor the information they transmit. Furthermore, the EU's Open Internet Regulation (2015/2120) bans ISPs from employing DPI for traffic management if it involves inspecting specific content like protocol payloads or domain names. To implement DPI, organizations must conduct a Data Protection Impact Assessment (DPIA) and prove that their use serves a "legitimate interest" without infringing on users' fundamental rights.
Meanwhile, in countries with strong privacy protections or authoritarian regimes, the use of DPI is either tightly restricted or heavily exploited for control.
Restrictions and Privacy Protections
Countries with robust privacy laws, such as Switzerland, place strict limits on DPI. For example, Article 23 of Switzerland's Arbeitsgesetz emphasizes privacy safeguards and restricts DPI for surveillance purposes. The Body of European Regulators for Electronic Communications (BEREC) has also stated that DPI is "very unlikely" to be legally used for traffic management, reflecting the EU's commitment to net neutrality.
On the other hand, authoritarian governments often leverage DPI as a tool for state control. China uses DPI extensively as part of its Great Firewall to filter content and terminate connections based on keywords. In Iran, authorities rely on DPI systems from companies like Nokia Siemens Networks to monitor, block, and potentially modify voice and data communications. Similarly, Pakistan has employed DPI technology from Canadian company Sandvine to filter content deemed blasphemous under the Prevention of Electronic Crimes Act (PECA). In Egypt, DPI was used by the National Telecom Regulatory Authority to block Signal in 2015 and later restrict VoIP services like FaceTime and WhatsApp in 2017. Russia, too, has embraced DPI, initiating a nationwide rollout in 2019, estimated to cost 20 billion roubles (around $300 million).
Comparison Table
Jurisdiction | Legal Status | Primary Use Cases | Key Regulatory Framework | Privacy Risk Level |
|---|---|---|---|---|
United States | Legally Permitted | Lawful intercept, cybersecurity, targeted ads | CALEA (Title 47, Subpart Z) | Moderate |
European Union | Restricted | Network management, security (with limitations) | GDPR, ePrivacy Directive, Regulation 2015/2120 | Low to Moderate |
China | State-Mandated | Censorship, political surveillance | Great Firewall (Golden Shield Project) | Very High |
Russia | Mandated/Expanding | Blacklist enforcement, surveillance | Federal Law No. 139, SORM | Very High |
Switzerland | Highly Restricted | Limited security applications only | Arbeitsgesetz (Labor Law), FADP | Low |
Pakistan | Permitted | Content filtering, blasphemy enforcement | Prevention of Electronic Crimes Act (PECA) | High |
Egypt | Permitted | VoIP blocking, encrypted app filtering | National Telecom Regulatory Authority oversight | High |
The global differences in DPI regulation spark debates over its ethical use. Democracies often focus on protecting privacy and maintaining net neutrality, while authoritarian regimes use the technology to control information and monitor citizens. These contrasting approaches highlight the tension between security needs and the preservation of individual freedoms.
Protecting Privacy: Decentralized Tools as a Solution
DPI laws differ widely across regions, but no matter where you are, this technology poses a serious threat to privacy. Thankfully, decentralized tools offer a way to counteract the invasive nature of DPI.
Decentralized VPNs and Borderless Networking
Traditional VPNs rely on centralized servers to route your internet traffic. While they provide some level of privacy, these servers create single points of failure that DPI systems can easily target and analyze. Decentralized VPNs (dVPNs) take a different approach, using a peer-to-peer network to distribute traffic across multiple nodes. This makes it much harder for DPI systems to intercept or block data.
One example is the MASQ VPN Network, which shifts away from corporate-controlled server farms. Instead, it allows users to "border-hop" across a global network of community-run nodes. Without a central authority or logging infrastructure, the metadata typically exploited by DPI systems becomes inaccessible. As Ben Wagner from Delft University of Technology pointed out, DPI could evolve from simply filtering online content to actively editing it. However, decentralized networks like MASQ eliminate the centralized control required for such interference. This makes MASQ a powerful tool for protecting online privacy.
The MASQ Ecosystem: A Complete Private Gateway
MASQ doesn't stop at being a dVPN. It’s the first fully integrated private internet gateway, bringing together three key components in one ecosystem:
MASQ Browser: A privacy-focused browser that avoids tracking and corporate influence. It also supports Handshake decentralized domains, which mainstream browsers typically overlook.
MASQ VPN Network: A peer-to-peer network that merges the strengths of VPNs and Tor, while avoiding the weaknesses of centralized systems.
Timpi Search: An independent search engine built on its own massive index, free from reliance on Google or Bing data.
Together, these tools create a seamless system that protects your data at every stage. From your initial search query to viewing a webpage, MASQ ensures your information stays private through encrypted browsing, decentralized traffic routing, and independent search.
Community-Powered Privacy
The internet was originally designed as a "dumb" network with "intelligent" endpoints, meaning it wouldn’t interfere with data. DPI reversed this concept, turning networks into "intelligent" systems that allow ISPs and governments to monitor and manipulate content. This shift undermines the open and egalitarian nature of the internet’s original design. Decentralized tools like MASQ aim to restore this balance, putting control back into the hands of users and preserving the internet's foundational principles of freedom and privacy.
Conclusion
The ethical and practical challenges of Deep Packet Inspection (DPI) reveal a tough balancing act between its security advantages and the risks it poses to privacy. While DPI enables real-time threat detection and network improvements, it also allows Internet Service Providers (ISPs) and governments to monitor, log, and even alter private communications. As technology writer Muhammad Raza aptly stated:
"The core issue is balancing the need for protection against ever-evolving cyber threats with an individual's right to privacy and control over their personal information".
This shift undermines the original vision of an open internet. DPI essentially transforms networks into surveillance hubs, granting third parties the ability to interfere with your data whenever they choose.
In a world where digital privacy is essential, allowing such manipulation of personal data threatens freedom of expression and access to information. However, decentralized solutions offer a way forward, bypassing these trade-offs entirely.
Decentralized tools return control of data to users. For example, MASQ provides a private internet gateway that combines a privacy-focused browser, a decentralized VPN network, and an independent search engine. It operates without central oversight, logging, or interference - delivering an internet experience that’s private, uncensored, and shaped by the community for those who prioritize privacy.
If reclaiming your online privacy matters to you, discover what MASQ has to offer at masqbrowser.com.
FAQs
Can DPI see my encrypted messages?
Deep Packet Inspection (DPI) has the ability to examine the content of unencrypted messages. However, when it comes to encrypted messages, DPI cannot access their content unless those messages are decrypted first - a process that DPI does not usually handle.
How is DPI different from normal packet inspection?
Deep Packet Inspection (DPI) goes beyond the surface-level analysis of standard packet inspection. While regular inspection focuses on packet headers - like IP addresses and protocols - DPI digs deeper, analyzing the entire data payload. This enables it to identify specific applications, enforce detailed policies, or detect potential threats.
Think of it this way: standard inspection is like reading the title and summary of a book, while DPI reads every page. This makes DPI far more detailed, but also much more invasive.
How can MASQ reduce DPI tracking?
MASQ takes a privacy-first approach by using a decentralized ecosystem to route internet traffic across the globe. Unlike traditional systems, it doesn't log or monitor user data, making it tough for Deep Packet Inspection (DPI) tools to track or analyze user activity. This method strengthens user privacy and security, shielding them from intrusive tracking techniques.




