
Decentralized VPNs (dVPNs) offer stronger privacy protection by addressing key weaknesses in traditional VPNs. Unlike VPNs, which rely on centralized servers and are vulnerable to logging, hacking, and subpoenas, dVPNs distribute traffic across independent nodes, making it nearly impossible to track or reconstruct user activity. Here’s how dVPNs safeguard your metadata:
No Centralized Logging: dVPNs eliminate single points of failure by spreading traffic across independent nodes, preventing comprehensive logging.
Multi-Hop Routing: Data passes through multiple nodes, ensuring no single node knows both the origin and destination.
Independent Node Operators: Nodes are managed by individuals globally, reducing the risk of centralized control or surveillance.
Decentralized Directory Authority: Network operations are managed via blockchain or smart contracts, removing central control points.
Dummy Traffic Generation: Randomized traffic patterns disguise real activity, thwarting surveillance and traffic analysis.
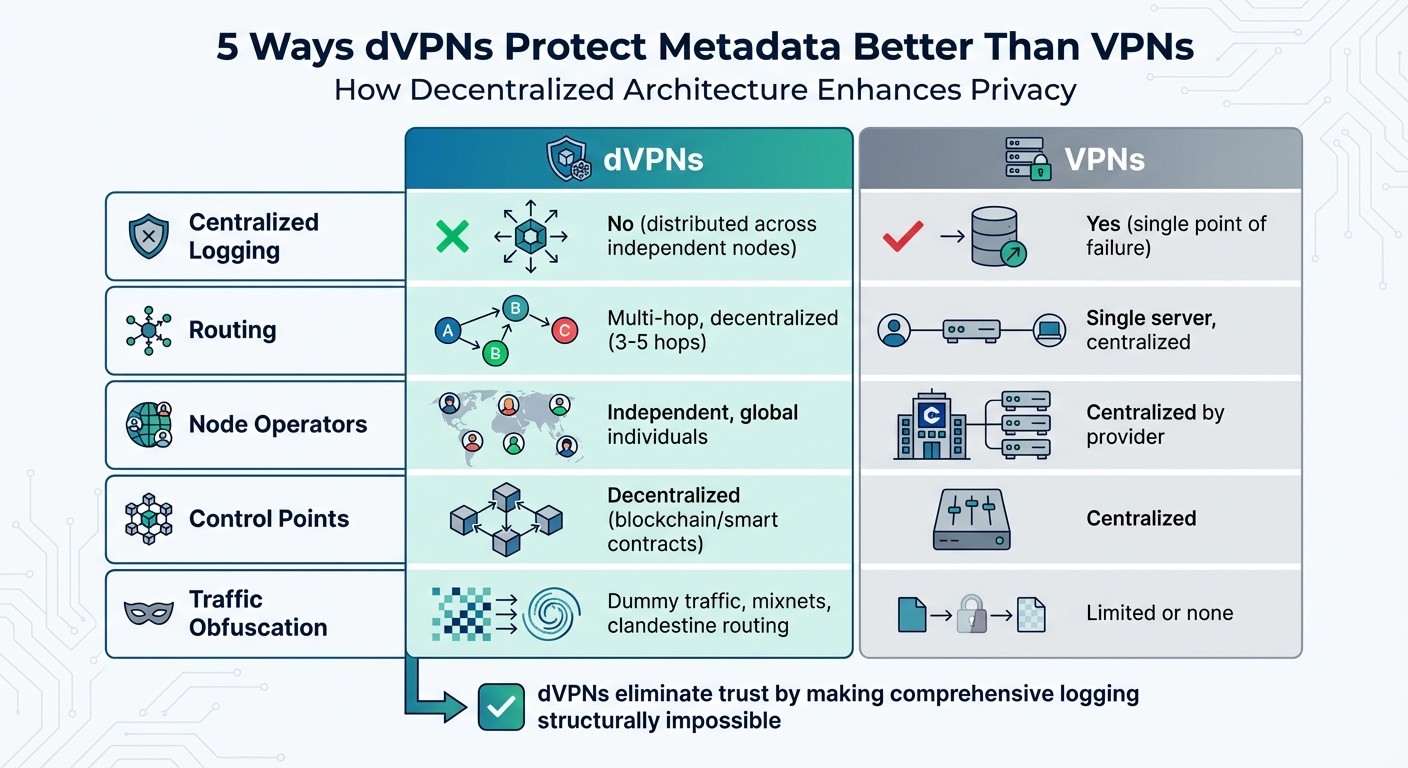
Quick Comparison
Feature | dVPNs | VPNs |
|---|---|---|
Centralized Logging | No | Yes |
Routing | Multi-hop, decentralized | Single server, centralized |
Node Operators | Independent, global | Centralized by provider |
Control Points | Decentralized (blockchain) | Centralized |
Traffic Obfuscation | Dummy traffic, mixnets | Limited or none |
dVPNs prioritize privacy by design, making them a stronger choice for protecting your online activity and metadata.
dVPN vs VPN Metadata Protection Comparison
VPN vs dVPN Explained: Privacy, Security & The Future of Online Anonymity
How dVPNs Protect Metadata Better
Traditional VPNs rely on centralized servers to route all your traffic. This setup creates a single point where your IP address, connection times, and browsing habits can be logged, leaving your data exposed to potential threats like hacking or subpoenas. This risk highlights the importance of a decentralized alternative.
dVPNs take a completely different approach by using a global peer-to-peer network of independent nodes. Unlike traditional VPNs, dVPN providers don’t own or control these nodes, which means they’re built to avoid creating a central log of user activity. Casey Ford, PhD, Communications Lead at Nym, emphasizes this:
It eliminates "central points of failure", meaning no single company can be hacked, subpoenaed, or coerced into handing over your data.
This decentralized structure scatters your metadata across numerous independent operators, ensuring no single node has access to your full digital activity.
In addition to node independence, dVPNs use advanced configurations to strengthen privacy. Blockchain-based smart contracts handle network settings instead of relying on a central server, removing another weak link. Mesh topologies allow the network to reroute traffic dynamically if a node is compromised. Plus, gossip protocols enable nodes to share routing information without revealing identifying details.
1. No Centralized Logging
Eliminating Single Points of Control
Traditional VPNs often rely on centralized servers to store connection data, making them a prime target for hackers or government subpoenas. Decentralized VPNs (dVPNs) tackle this issue by spreading control functions - like node discovery and payment processing - and routing data across thousands of independently operated nodes. This structure significantly boosts metadata security. As Casey Ford, PhD, Communications Lead at Nym, puts it:
"Decentralized VPNs aim to solve trust issues by distributing risk instead of having to put your faith into any one provider or parent company."
How Decentralization Prevents Logging
The decentralized nature of dVPNs makes comprehensive logging virtually impossible. Each node operator typically processes only about 1/100th (or even less) of the network's total traffic. On top of that, the data remains encrypted and inaccessible without complete access to the entire network. This fragmentation ensures that no individual or organization can piece together your full browsing history.
Built-In Defense Against Censorship and Surveillance
By eliminating centralized control points, dVPNs naturally resist censorship and surveillance. Governments or other entities cannot target a single server to disrupt the network or demand access to user data. This design makes it far more difficult for legal or political pressures to compromise your privacy, offering a more secure and private browsing experience.
2. Multi-Hop Routing
Enhanced Anonymity Through Routing Techniques
Multi-hop routing introduces a level of privacy that standard VPNs simply can't match. When using a dVPN, your data doesn't just pass through a single server - it moves through multiple independent nodes before reaching its final destination. Here's how it works: the entry node knows your IP address but has no clue where your data is headed. The exit node, on the other hand, knows the destination but can't trace it back to you. Meanwhile, the relay nodes in between are completely in the dark about both ends of the connection.
By default, MASQ uses a 3-hop route to ensure no single node can piece together your origin and endpoint. For even greater privacy, there's a 5-hop mixnet mode that fragments data packets even further, making it nearly impossible for anyone to reconstruct your online activity .
On top of this routing system, additional obfuscation techniques make tracking your activity even harder.
Obfuscation of User Activity
Advanced dVPNs don't stop at routing - they also use obfuscation to make surveillance incredibly challenging. For instance, mixnet technology scrambles the order of data packets and adds fake traffic that looks identical to real data. This makes it tough for adversaries to use timing or volume analysis to figure out what you're doing online. MASQ goes a step further with "clandestine routing", which disguises your data packets to look like ordinary HTTPS traffic. This clever approach thwarts packet sniffing and deep packet inspection, allowing your traffic to blend in with everyday internet activity.
These routing and obfuscation methods are further strengthened by the decentralized nature of dVPNs.
Decentralized Infrastructure for Data Handling
The real power of multi-hop routing lies in its decentralized design. Unlike traditional VPNs that rely on centralized servers, dVPNs spread traffic across a network of independent nodes. This decentralized model ensures that no single entity has access to your entire browsing history, making it immune to subpoenas or targeted hacking attempts.
3. Independent Node Operators
Elimination of Centralized Control Points
Unlike traditional VPNs, dVPNs rely on a network of independent node operators scattered across the globe. These operators, often everyday users, share their bandwidth in exchange for cryptocurrency rewards. This decentralized approach eliminates the possibility of a single entity reconstructing your browsing history.
Casey Ford, PhD, Communications Lead at Nym, explains it well:
With a centralized VPN, you have to trust that the provider is telling the truth... but with a decentralized VPN, logging user behavior is much more difficult because the nodes are operated independently.
This independence ensures a level of privacy and security that centralized VPNs simply can't match.
Decentralized Infrastructure for Data Handling
dVPNs are designed with structural unloggability in mind. Temporary session keys and payment receipts exclude activity metadata, ensuring your online behavior remains private. Each node only interacts with its immediate neighbors - usually about five - creating neighborhood isolation. This means no single node can map the entire network or trace the full path of your data, making it nearly impossible to piece together your activity.
The system also separates the control plane (handling discovery and payments on-chain) from the data plane (where encrypted traffic flows off-chain). This separation ensures that your browsing data never touches the public blockchain, keeping it fully private. Combined with multi-hop routing, this setup makes tracking user activity an incredibly complex task.
Resistance to Censorship and Surveillance
The global distribution of independently operated nodes makes shutting down a dVPN network nearly impossible. Even if authorities manage to block or seize some nodes, your traffic can seamlessly reroute through other available operators. There’s no central hub to raid, no executive to arrest, and no server farm to take offline. When comparing dVPNs, VPNs, and Tor, this jurisdictional resilience gives dVPNs a significant edge over traditional VPNs in resisting government censorship and surveillance efforts.
4. Decentralized Directory Authority
Independent nodes in dVPNs not only prevent centralized logging but also rely on a decentralized directory authority to spread network control. This authority consists of a group of nodes responsible for monitoring the network's health and configuration. Unlike Traditional VPNs, which are managed by a single entity, this decentralized setup eliminates a central point of failure. When considering if you need a VPN or a more robust alternative, making the network less vulnerable to hacks and legal demands.
Elimination of Centralized Control Points
Instead of centralized servers, dVPNs utilize blockchain technology or smart contracts to coordinate network operations. This design removes the need for a central database of user connections, significantly reducing the risk of exploitation by adversaries. By distributing control across the network, dVPNs avoid the vulnerabilities associated with single-provider models.
Decentralized Infrastructure for Data Handling
dVPNs separate the network's control plane from its data plane. The control plane manages node discovery and accounting using on-chain registries, while encrypted user traffic is handled securely off-chain on the data plane.
For instance, some dVPNs leverage Nym's Nyx blockchain to manage directory authority through smart contracts. This ensures that network health and node availability are monitored without granting any central entity the ability to log or inspect user activity.
Resistance to Censorship and Surveillance
By removing centralized control, dVPNs eliminate the possibility of being compelled to disclose user data. Traditional VPNs can be forced by court orders or local laws to share user information. In contrast, decentralized directory authorities lack a single company or office that can be subpoenaed or targeted.
Additionally, the distributed structure of blockchain-based directory authorities ensures that even if certain nodes are blocked, the network remains operational through other independent nodes. This resilience makes it difficult for adversaries to disrupt the system entirely.
5. Dummy Traffic Generation
Obfuscation of User Activity
Dummy traffic generation adds a layer of metadata protection that traditional VPNs can't offer. Known as "clandestine routing" in decentralized VPNs (dVPNs), this technique camouflages your online activity by mixing it with random traffic patterns. The result? Observers are left guessing, unable to separate your real actions from the background noise.
"By masking packages in random traffic patterns, it deters typical packet sniffing and traffic analysis methods, and prevents the blocking of requests." - MASQ Network Documentation
This process lays the groundwork for even stronger anonymity measures.
Enhanced Anonymity Through Routing Techniques
While traditional VPNs rely on a single proxy, they can still be vulnerable to timing and packet size correlation attacks. If someone monitors both the entry and exit points of the VPN, they might be able to piece together your activity despite encryption. Decentralized networks counter this by generating cover traffic across a web of independent nodes, effectively dismantling attempts to reconstruct your actions.
MASQ, for instance, uses clandestine routing to disguise CORES (Client-Origin-Relay-Exit-Server) packages with random patterns. This approach conceals both the type of traffic and the application being used. When combined with multi-hop routing, no single node has access to both the origin and destination of your data. This decentralized setup makes tracking nearly impossible.
Resistance to Censorship and Surveillance
Cover traffic is a powerful tool against surveillance methods like deep packet inspection (DPI) and AI-based traffic analysis. By blending encrypted data with regular HTTPS traffic, dVPNs make it challenging for censors to identify and block VPN protocols. Additionally, timing protection and delay obfuscation help shield users from large-scale state surveillance.
For those in heavily monitored environments, this level of protection is game-changing. Traditional VPNs, with their identifiable traffic patterns, can be detected and blocked. In contrast, dVPNs with dummy traffic generation remain hidden, ensuring that your connection stays secure and accessible, even under the most restrictive conditions.
Conclusion
Decentralized VPNs (dVPNs) are changing the game for metadata protection by shifting trust from centralized servers to a network of independent nodes. This design makes comprehensive logging technically impossible, not merely a matter of corporate promises. As Casey Ford, PhD, Communications Lead at Nym, puts it:
A dVPN is a peer-to-peer privacy network that replaces centralized corporate servers with a distributed architecture of independent nodes.
The key difference lies in the approach to trust. Traditional VPNs rely on their "no-logs" policies, asking users to take their word for it. In contrast, dVPNs ensure logging is structurally impossible. This technical framework forms the backbone for platforms like MASQ.
MASQ takes these principles further with practical innovations. By routing traffic through distributed residential IPs and using stealthy techniques to blend data with regular HTTPS traffic, MASQ makes it much harder for governments or other entities to block access. Users who share bandwidth earn $MASQ tokens, creating a self-sustaining system without the need for central servers. Additionally, features like integrated Web3 wallets, native ENS domain resolution, and a decentralized dApp store bring privacy tools directly into the browsing experience.
The MASQ Network, once live, will grow to a point where it cannot be shutdown. No large entity or Government could censor the network from allowing users to access the freedom of the entire Internet. - MASQ Network Documentation
This decentralized approach not only protects metadata but also gives users more control over their digital presence, fostering a greater sense of security and freedom online.
FAQs
How do decentralized VPNs protect your data from being logged?
Decentralized VPNs, or dVPNs, take a different approach to securing your online activity. Instead of routing your internet traffic through centralized servers like traditional VPNs, they use a network of distributed nodes run by individual users. This setup removes the reliance on a single control point, reducing the risk of data collection or monitoring.
Because there’s no central authority, dVPNs make it much tougher for anyone to track or log what you’re doing online. This added layer of privacy helps keep your metadata secure and shields it from surveillance or unauthorized access.
What is multi-hop routing, and how does it improve privacy in decentralized VPNs?
Multi-hop routing is a technique used by decentralized VPNs (dVPNs) to boost privacy by routing your data through several nodes before it reaches its final destination. Each node applies an additional layer of encryption, making it significantly harder for anyone to track or intercept your online activity.
This method effectively masks your IP address and other metadata, offering stronger anonymity and shielding you from surveillance or censorship. With networks of user-operated nodes, dVPNs like MASQ let you browse the internet securely and privately, free from tracking or interference.
Why do independent node operators play a key role in dVPN privacy?
Independent node operators play a crucial role in ensuring the privacy of decentralized VPNs (dVPNs). By creating a decentralized, peer-to-peer network, they eliminate the need for centralized servers. This setup prevents any single entity from controlling the network, reducing risks like surveillance, data logging, or censorship.
These operators enhance privacy by routing traffic through multiple independent points using techniques like multi-hop routing. This approach makes it significantly harder for third parties to trace or block user activity. The decentralized structure also ensures the network remains resilient against outages or targeted censorship, providing users with uninterrupted access and a higher level of anonymity. Furthermore, since node operators only handle fragments of traffic and do not maintain centralized logs, the risk of data collection is greatly reduced - offering a clear edge over traditional VPNs.
To keep the network strong and diverse, node operators are often incentivized, such as earning tokens in exchange for sharing their bandwidth. This reward system not only encourages participation but also helps maintain a secure and reliable network for all users.




