February 24, 2026

Decentralized VPNs (dVPNs) are changing how online privacy works by removing the risks tied to centralized servers. Unlike regular VPNs, which depend on a single company to protect your data, dVPNs use a peer-to-peer network of independent nodes. This setup makes it harder for governments or hackers to track, block, or compromise your internet activity. Key benefits include:
No central point of failure: dVPNs spread traffic across many nodes, reducing risks of breaches or shutdowns.
Better anonymity: Multi-hop routing ensures no single node can trace your origin and destination.
No personal data required: Payments are made through blockchain wallets, eliminating the need for emails or credit cards.
Censorship resistance: Residential IPs make it harder for websites or governments to block access.
These features make dVPNs a strong alternative for users concerned about security, censorship, and privacy in 2026.
VPN vs dVPN Explained: Privacy, Security & The Future of Online Anonymity
How Decentralized VPNs Improve Privacy Standards
Decentralized VPN vs Traditional VPN: Key Differences in Privacy and Security
Key Features of Decentralized VPNs
Decentralized VPNs take a completely different approach to online privacy by removing the reliance on centralized servers. Without a single repository for browsing data, this system eliminates the vulnerabilities often associated with traditional privacy tools.
Features like ephemeral session keys and off-chain accounting ensure that critical metadata is excluded, making it technically impossible to piece together a user's browsing history.
Multi-hop routing adds another layer of security by splitting the trust between nodes. Entry nodes only see your IP address, while exit nodes only know your destination. This design ensures no single node can connect your identity to your activity. Additionally, dVPNs use a variety of residential IP addresses, making your traffic appear as if it’s coming from regular users rather than a data center.
Web3 integration further enhances anonymity by allowing access through blockchain tokens and wallets, removing the need for personal information. With a pay-as-you-go model, users gain flexibility without being tied to recurring subscriptions.
These advancements highlight the stark differences between decentralized VPNs and their traditional counterparts.
Decentralized VPNs vs. Traditional VPNs
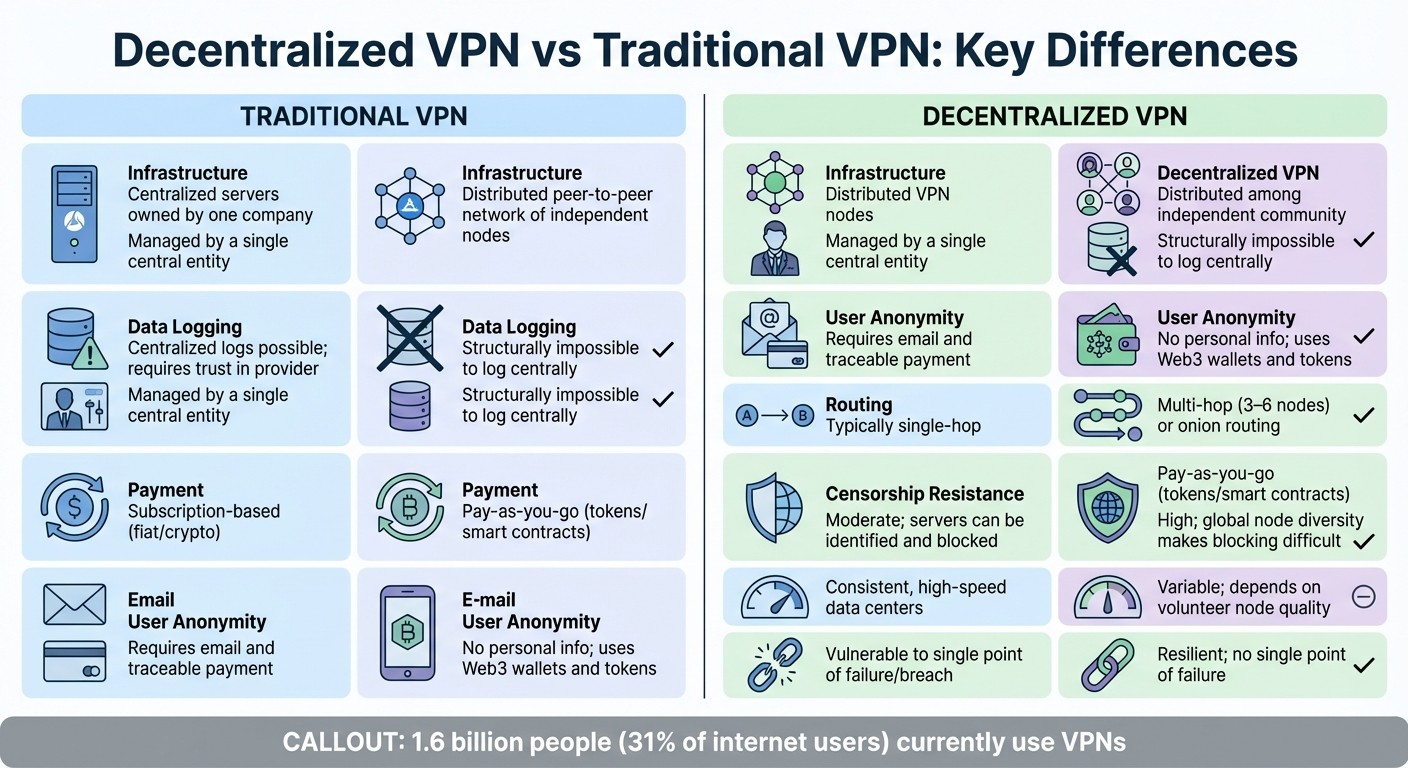
The table below compares how decentralized VPNs stack up against traditional VPN models in terms of privacy and trust.
This comparison underscores how decentralized VPNs address the weaknesses found in conventional VPN setups. Traditional VPNs rely on trust - especially with their "no-logs" policies - but decentralized VPNs eliminate the need for trust entirely by making centralized logging impossible. With around 1.6 billion people (31% of internet users) currently using VPNs, understanding these differences is essential for anyone prioritizing online privacy.
Common Tasks Enhanced by Decentralized VPNs
Decentralized VPNs (dVPNs) do more than just protect your data - they can improve how you interact with the internet daily. Here are some key activities that benefit from dVPNs:
Streaming Geo-Blocked Content
Platforms like Netflix, YouTube, and Google often limit content based on your location. Decentralized VPNs tackle this by routing your traffic through residential IP addresses instead of the easily identifiable data center servers. This makes your connection appear as if it’s coming from a regular home internet user, making it harder for streaming services to detect and block.
The multi-hop architecture offered by dVPNs ensures that streaming platforms can’t trace your requests back to you while keeping the connection stable. To optimize streaming, try these steps:
Use at least 3 hops to obscure your traffic.
Enable DNS-over-HTTPS to hide your DNS requests.
Test for potential leaks with tools like ipleak.net.
Keep browsing profiles separate - one for anonymous streaming and another for personal accounts to avoid cookie-based identity exposure.
These measures not only unlock geo-restricted content but also enhance your privacy and security while streaming.
Accessing Censored Websites
Censorship can block access to certain websites, but decentralized VPNs bypass these restrictions by routing your traffic through a flexible network of residential nodes. This approach hides your connection from Deep Packet Inspection (DPI) tools, making it almost impossible for authorities to block access. The distributed nature of dVPNs ensures there’s no central point of failure for censors to target.
"MASQ 3-hop route is the default minimum recommended route length for untraceable... traffic across the MASQ Network."
For safer browsing in restricted areas, enable content filtering with trusted DNS services like Cloudflare Family. Additionally, the pay-as-you-go model using utility tokens eliminates the need for traditional subscriptions, which might be monitored or blocked. Beyond bypassing censorship, dVPNs also secure interactions within the Web3 ecosystem.
Using Web3 Applications Securely
Decentralized VPNs are built to integrate seamlessly with Web3 applications. They support decentralized protocols like ENS and IPFS and often include built-in Web3 wallets (e.g., MetaMask, Frame) for secure, account-free authentication. This alignment with Web3 principles ensures a trustless and private online experience.
When engaging in activities like NFT trading or using DeFi platforms, your IP address can expose your location and identity to those analyzing blockchain data. A dVPN hides your IP during transactions, reducing the risk of targeted attacks and keeping your activities private.
What’s more, dVPNs embrace Web3’s decentralized ethos through their incentive model. Instead of simply paying for bandwidth, you can earn cryptocurrency tokens (such as $MASQ) by sharing your unused internet connection. This creates a self-reliant ecosystem where users contribute to the network rather than enriching a single corporation. For added privacy, it’s wise to use separate wallets for earning tokens (via bandwidth sharing) and spending tokens (for data usage).
How to Start Using a Decentralized VPN
Getting started with a decentralized VPN is simple and doesn’t require any technical expertise. You’ll just need to download the software, set up your wallets, and you’ll be ready to browse privately in no time.
Setup Guide
To begin, head to masqbrowser.com and download the MASQ browser from the official site. This is crucial for your security. The software is compatible with Windows, MacOS, and Linux, so it works regardless of your operating system. After downloading, verify the installer checksums to ensure the file’s integrity.
The onboarding process is user-friendly and walks you through connecting to the MASQ Network. No special hardware or complicated setup is required. During setup, you’ll need to create two wallets: one for paying for services and another for receiving payments. It’s best to create new wallets instead of importing existing ones - this keeps your dVPN activity completely separate from other cryptocurrency transactions and adds an extra layer of privacy.
Before jumping into the mainnet, test the network on Base Sepolia or Polygon Amoy using tMASQ tokens. This lets you explore the features risk-free and get a feel for the system.
After connecting, visit ipleak.net to confirm that your IP and DNS are hidden. The MASQ browser also supports ENS (Ethereum Name Service), IPFS content, and includes a built-in dApp store for accessing Web3 applications. For secure and anonymous transactions, you can link wallet extensions like MetaMask, Frame, or Phantom.
Once everything is set up, you can enhance your privacy with specific performance settings.
Tips for Better Privacy and Security
After setup, you can optimize your MASQ experience with some key privacy and security features.
One of the most critical settings is multi-hop routing. MASQ allows 1 to 5 hops, but 3 hops strikes a good balance between privacy and performance. With 3-hop routing, no single node can identify both the origin and destination of your traffic. On average, this setting provides between 700–1,000 GB per $MASQ token.
Enable clandestine routing to disguise your data as normal HTTPS traffic, which helps bypass deep packet inspection tools often used by ISPs and censors. Additionally, you can tweak content filtering in the MASQ Dashboard. For instance, switching to Cloudflare Family DNS adds family-friendly filtering while preventing your ISP from tracking which domains you visit.
If you’re interested in earning tokens by sharing bandwidth, you can activate "Earn Mode." This allows you to contribute your unused internet connection to the network. However, keep in mind that only one MASQ node can operate per public IP address. To maintain privacy, it’s a good idea to keep separate wallets for earning and spending activities.
Lastly, make sure to regularly update your software and use separate profiles for anonymous and personal browsing. This helps prevent cookies and tracking scripts from linking your activities across sessions.
Conclusion: The Future of Online Privacy With Decentralized VPNs
With censorship tightening, ISP tracking becoming more invasive, and traditional VPNs facing increasing restrictions, the internet is at a crossroads. The way forward? Decentralized VPNs, which shift control from corporations to individual users.
MASQ’s dMeshVPN architecture is a game-changer in this space. By routing traffic through a distributed network of user-operated nodes using residential IPs, it eliminates centralized points of failure. This approach makes the network incredibly resilient - hard to block, blacklist, or take down. Plus, by blending with normal internet traffic, decentralized VPNs avoid detection and ensure seamless, uninterrupted use.
Key features like multi-hop routing add another layer of security, ensuring no single node can trace both the origin and destination of your data. On top of that, clandestine routing disguises VPN traffic as standard HTTPS, offering real anonymity in practice.
What truly sets this apart is its self-sustaining design. Users who share their bandwidth earn $MASQ tokens, creating a system that grows stronger as participation increases. This isn’t just about hiding IP addresses - it’s about building a censorship-resistant internet where no single entity holds the keys.
These advancements are reshaping online privacy by removing the need to rely on centralized authorities. Instead, they empower users with decentralized infrastructure, community-driven governance, and the security of cryptographic protocols. As surveillance expands and censorship becomes more aggressive, decentralized solutions are becoming essential to protect internet freedom.
FAQs
Are dVPNs legal in the United States?
Yes, decentralized VPNs (dVPNs) are legal in the United States. They align with current laws and aim to improve users' online privacy and security.
How do I pick the right hop count for speed vs privacy?
Decentralized VPNs, or dVPNs, rely on multi-hop routing to boost privacy. Essentially, your internet traffic passes through multiple nodes, making it harder to trace. However, there’s a trade-off: more hops mean slower connection speeds.
If you're aiming for top-tier privacy and want to bypass censorship effectively, using 3 or more hops is a solid choice. Just keep in mind, this setup can noticeably impact your browsing speed. On the other hand, for quicker browsing while still maintaining decent privacy, sticking to 1-2 hops should do the trick.
Ultimately, the right setup depends on what matters more to you - speed or security. Some dVPNs even allow you to tweak this balance to suit your specific needs.
What are the risks of earning tokens by sharing bandwidth?
When you earn tokens by sharing bandwidth in a decentralized VPN network, there are a few risks to keep in mind. For one, if the network's security measures are compromised, it could leave you vulnerable to cyber threats. There's also the chance that your shared bandwidth might be misused if the network's privacy protocols aren't clear or reliable. Another concern is the potential for your bandwidth to be exploited for illegal activities, which could result in legal troubles or harm your reputation.
To minimize these risks, it's crucial to ensure the network you join has strong security measures and transparent privacy policies in place. Always do your homework before participating.




