
Zero-knowledge proofs (ZKPs) are transforming Web3 by allowing users to verify information without exposing sensitive data. This cryptographic method ensures privacy while maintaining trustless verification, addressing key challenges of public blockchains like transaction transparency and pseudonymity risks. Here's why they matter:
Private Transactions: ZKPs validate transactions without revealing amounts, balances, or participants. For instance, Zcash and Aztec Network use ZKPs to secure DeFi transactions while reducing costs by up to 200x.
Decentralized Identity: ZKPs enable selective disclosure, letting users prove attributes (e.g., age or citizenship) without sharing full personal details. Bhutan's National Digital ID and zkMe are examples of this in action.
Privacy in dApps: Smart contracts powered by ZKPs verify on-chain logic without exposing inputs, enhancing user privacy in governance, authentication, and more.
Despite challenges like high computation costs and trusted setup risks, advancements like hardware acceleration, recursive proofs, and transparent setups are making ZKPs more efficient. Platforms like zkSync Era and Polygon zkEVM are driving adoption by simplifying development.
ZKPs are reshaping Web3 by prioritizing privacy and security, moving from "don't be evil" to "can't be evil" models. Whether it's shielding transactions, verifying identities, or enabling private dApps, ZKPs are central to the evolution of decentralized systems.
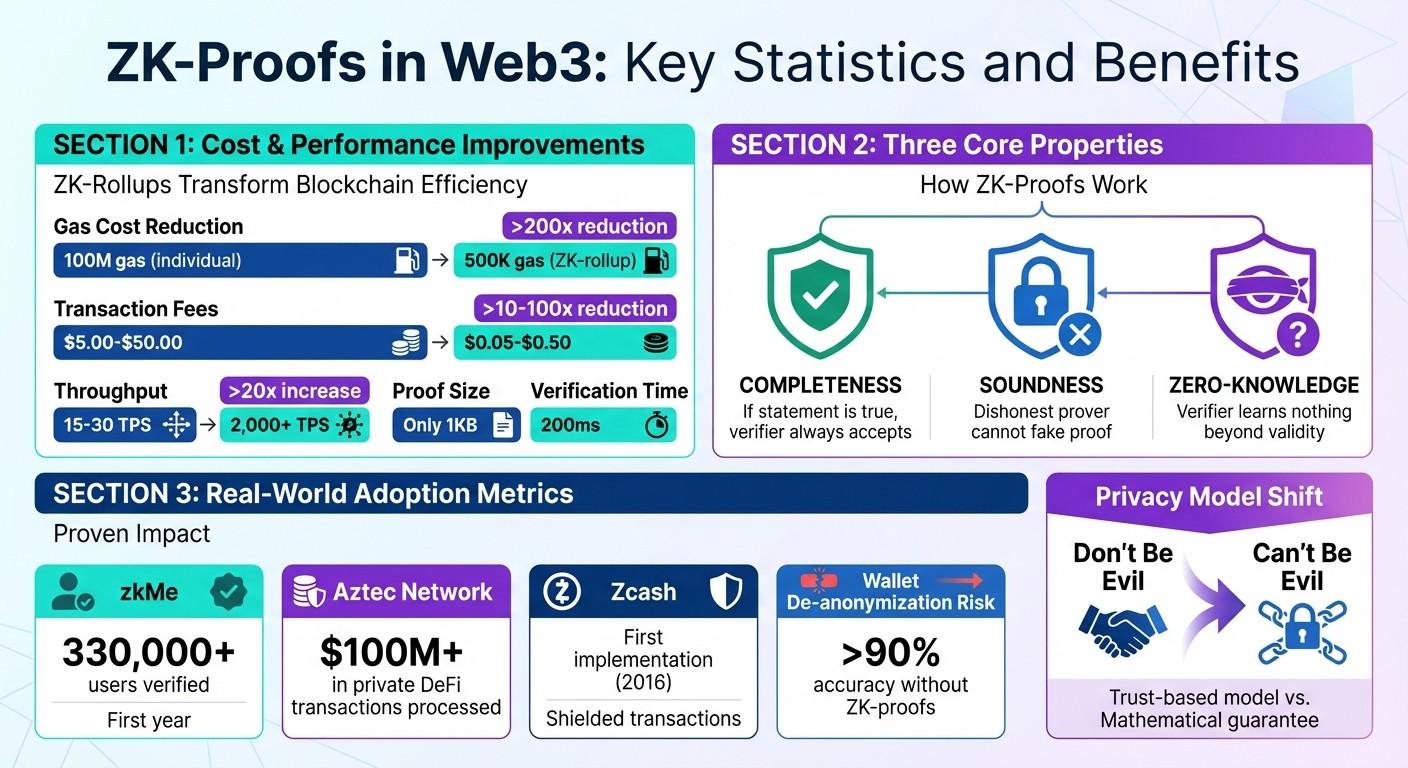
ZK-Proofs Impact on Web3: Key Statistics and Benefits Comparison
What Are Zero-Knowledge Proofs?
Definition and Core Concepts
A zero-knowledge proof (ZKP) is a cryptographic technique that enables one party, known as the prover, to demonstrate the truth of a statement to another party, the verifier, without revealing any supporting data. This concept was first outlined in a 1985 paper, which described it as:
"A zero-knowledge protocol is a method by which one party (the prover) can prove to another party (the verifier) that something is true, without revealing any information apart from the fact that this specific statement is true."
ZKPs rely on three essential properties:
Completeness: If the statement is true, the verifier will always accept the proof.
Soundness: A dishonest prover cannot trick the verifier with a fake proof.
Zero-knowledge: The verifier learns nothing beyond the validity of the claim.
These principles ensure that sensitive data remains private while still enabling verification through mathematical certainty.
How the Verification Process Works
The verification process revolves around three main elements: the witness (secret information known only to the prover), the challenge (a test set by the verifier), and the response (the prover's reply that confirms their knowledge).
In interactive proofs, the verifier and prover engage in multiple rounds of interaction. For example, imagine a verifier asking the prover to navigate a maze. By issuing random challenges like choosing an exit, the verifier can confirm the prover's knowledge without needing to see the entire maze.
However, modern systems - especially in blockchain applications - favor non-interactive zero-knowledge proofs (NIZKPs). These proofs are self-contained, meaning they can be verified at any time without requiring back-and-forth communication. This approach is ideal for decentralized systems, where constant interaction isn't feasible. Think of it like showing only "Waldo's face" on a crowded map by using a cutout - proving you found Waldo without revealing the rest of the scene. Similarly, NIZKPs validate claims while keeping all other details hidden.
Zero-Knowledge Proofs Explained: Privacy in Blockchain (zk-SNARKs & zk-STARKs)
How ZK-Proofs Protect Privacy in Web3
After understanding the basics of ZK-proofs, it's time to see how they safeguard privacy in Web3 applications.
Private Transactions
ZK-proofs make it possible to validate cryptocurrency transactions without revealing sensitive financial details. Normally, when you send cryptocurrency, the network must confirm that you have enough funds and aren't using the same coins twice. This process traditionally required making balances and transaction amounts visible to everyone.
ZK-proofs tackle this by converting transaction rules into arithmetic circuits. Your device processes your private data through the circuit and produces a cryptographic proof. This proof confirms you have sufficient funds and ensures no double-spending - without ever exposing your balances or transaction amounts.
The efficiency gains are striking. For example, verifying 1,000 transactions individually on Ethereum could cost 100 million gas. In contrast, a single ZK-rollup proof for those same transactions costs around 500,000 gas - a 200x reduction in cost. Zcash, which launched in 2016, was an early adopter of this approach with its "shielded" transactions. These transactions hide the sender, receiver, and amount while still preventing double-spending. More recently, Aztec Protocol's zk.money application has processed over $100 million in private DeFi transactions. Using zk-SNARKs, it shields transaction details while enabling users to interact with public protocols like Uniswap.
Decentralized Identity Verification
ZK-proofs also enable selective disclosure, allowing you to prove specific facts about yourself without revealing unnecessary personal data. For instance, instead of sharing your full birthdate, passport number, or tax ID, you can use a ZK-proof to confirm statements like "I am over 18" or "I am a U.S. citizen."
This concept empowers individuals through self-sovereign identity (SSI). One compelling example is Bhutan's National Digital ID system, implemented on Ethereum between 2023 and 2026. This system lets citizens prove their age or citizenship for government services without exposing sensitive details. Similarly, the World ID Protocol uses ZK-proofs to verify that users are unique humans (via iris scans) without linking the verification to their identity or storing biometric data on a public ledger.
The impact of decentralized identity systems is already evident. For instance, zkMe has provided identity verification for over 330,000 users in its first year. This is crucial because public wallet addresses can often be de-anonymized with more than 90% accuracy using on-chain heuristics. Privacy-preserving identity verification is, therefore, essential for Web3 adoption.
Privacy-Focused Decentralized Applications
Beyond transactions and identities, decentralized applications (dApps) are now using ZK-proofs to power private smart contracts. These contracts allow on-chain logic and state changes to be verified without exposing inputs or contract code to the public. This shifts the focus from trusting entities to relying on mathematically enforced privacy.
For example, zkPass launched TransGate, a tool that uses ZK-proofs and Multi-Party Computation to authenticate data from HTTPS websites - such as bank balances or social media profiles - without requiring users to share login credentials. Similarly, ING Bank has applied ZK-proofs to confirm mortgage eligibility by verifying that clients meet specific financial thresholds without exposing raw financial details on a shared ledger.
ZK-proofs also enhance privacy in governance. Protocols like MACI (Minimum Anti-Collusion Infrastructure) use ZK-proofs to hide individual votes in decentralized governance systems while ensuring the final tally is mathematically accurate. To put this into perspective, a typical zk-SNARK proof is only about 1KB in size and can be verified in just 200ms, making these privacy measures practical for real-world applications.
Benefits of ZK-Proofs for Web3 Users
ZK-proofs bring a new level of privacy and security to Web3, offering users a way to interact with decentralized applications without sacrificing sensitive information. By eliminating the need for intermediaries and safeguarding personal data, these advancements are already reshaping how people engage with blockchain technologies.
Privacy Without Trusting Intermediaries
Most traditional Web3 applications operate on a "don't be evil" principle, where users trust that companies will handle their data responsibly. ZK-proofs completely change this dynamic by introducing a "can't be evil" model. Instead of relying on trust, users share only a mathematical proof that verifies a statement's truth - without revealing any underlying data.
"Zero-knowledge architectures introduce an unprecedented level of verifiable data privacy, fostering user trust." – TokenMinds Team
This approach ensures that your private information remains inaccessible, even to the service provider. The network validates the proof alone, leaving your data untouched. This also means you can verify permissions - like proving you're authorized to perform an action - without exposing your identity. It's a game-changer for privacy and data handling.
Enhanced Data Security
ZK-proofs significantly reduce the risks associated with centralized data storage. Since zero-knowledge systems don't store raw data on servers, even if a provider experiences a breach, your information stays protected. This design also minimizes insider threats, as employees and administrators can only access cryptographic proofs, not the actual data. The result? A safer, more secure environment for Web3 users.
Examples of ZK-Proof Implementation
MASQ: Private Web3 Access
MASQ combines zero-knowledge principles with a decentralized approach to create a powerful privacy ecosystem. It offers a peer-to-peer VPN, a privacy-focused browser, and an independent search engine - all working together seamlessly.
The VPN ensures global traffic is routed without storing any user data. Meanwhile, the browser supports Handshake’s decentralized domains and features Timpi Search, an independent search index known for its depth. This setup guarantees private searches without profiling or tracking.
In 2026, MASQ joined forces with Timpi to form a unified, community-driven internet gateway. This merger allowed users to fully manage their data, from browsing to network routing, making MASQ a standout example of ZK-proof applications in Web3 privacy.
Other Web3 Privacy Applications
MASQ isn’t the only platform harnessing zero-knowledge technology to enhance privacy. Here are a few other notable examples:
zkMe: Uses Groth16 zk-SNARKs to issue Soul Bound Tokens (SBTs), enabling privacy-centric identity verification.
Zcash: Pioneered shielded transactions, which hide details like the sender, recipient, and transaction amounts, offering an early and practical application of ZK-proofs.
Aztec Network: Through its zk.money protocol, processed private DeFi transactions exceeding $100 million, highlighting how zero-knowledge technology can safeguard assets on a large scale.
These examples demonstrate the growing adoption of ZK-proofs in creating secure and private solutions across the Web3 ecosystem.
Challenges and Future Development
Technical and Computational Limitations
Zero-knowledge proofs (ZKPs) still face a range of challenges that hinder their broader adoption. For one, generating these proofs can be computationally intensive. For example, creating proofs for something as simple as age verification might take 100–500 milliseconds, while more complex tasks like private transactions can require 5–15 seconds on current hardware. These delays make it difficult to integrate ZKPs into real-time systems where users expect near-instant responses.
Another issue is the high cost of on-chain verification. zk-SNARK proofs typically consume between 250,000 and 350,000 gas, while zk-STARK proofs can require anywhere from 1 to 2 million gas. Such costs make it less feasible to use these technologies for everyday transactions.
Trusted setups also pose a significant risk in many zk-SNARK systems. If the secret parameters - commonly referred to as "toxic waste" - aren’t securely destroyed after the setup process, there’s a risk that bad actors could exploit the system by creating fraudulent proofs. Additionally, developing and debugging ZK circuits is no small feat. It requires highly specialized cryptographic knowledge, and even small mistakes, like neglecting a range check, can lead to catastrophic system failures.
These obstacles have spurred ongoing innovation aimed at overcoming these limitations.
Emerging Solutions and Improvements
Despite the challenges, there’s steady progress in making ZKPs more efficient and accessible. Hardware acceleration using specialized chips like ASICs and FPGAs is one promising avenue. These chips can handle millions of proof rounds per second while consuming significantly less energy than traditional CPUs. This could potentially cut proof generation times from seconds down to milliseconds.
Recursive proofs are another game-changer. They allow one ZK-proof to validate another, enabling thousands of individual proofs to be combined into a single, compact proof. This approach greatly enhances scalability. For instance, ZK-Rollups can lower Ethereum gas fees by 10 to 100 times compared to regular mainnet transactions.
Newer proof systems are also addressing the issue of trusted setups. zk-STARKs and some implementations of PLONK now offer "transparent" setups, eliminating the toxic waste risk entirely. These systems also provide resistance to quantum computing threats. Moreover, platforms like Polygon zkEVM and zkSync Era, both launched in March 2023, are making ZK technology more accessible. They allow developers to deploy existing Solidity code on ZK-rollups with minimal modifications. This compatibility significantly lowers the technical barriers, enabling more developers to build privacy-focused applications without needing deep cryptographic expertise.
Conclusion
Zero-knowledge proofs (ZKPs) are reshaping privacy in Web3, offering a way to keep data confidential while still enabling reliable verification. They move the ecosystem from a "don't be evil" approach - relying on trust that companies won't misuse data - to a "can't be evil" approach, where privacy is secured through mathematical guarantees. This shift is redefining how digital ownership and verification function in the Web3 space.
ZK-Rollups are a standout example of the power of ZKPs. They dramatically cut Ethereum gas fees by 10–100×, increase throughput from 15–30 transactions per second (TPS) to over 2,000 TPS, and reduce transaction costs from $5.00–$50.00 to just $0.05–$0.50. Additionally, selective disclosure techniques allow users to prove specific attributes without revealing unnecessary details about their data.
"Zero-knowledge proofs are undeniably a cornerstone of Web3's evolution." - CryptoIndustry
The technology is already proving its worth. By early 2024, zkMe had enabled private identity verification for more than 330,000 users, while Aztec's zk.money facilitated over $100 million in private DeFi transactions.
MASQ is taking these advancements a step further by creating a fully private gateway to Web3. It combines several tools into one ecosystem: the MASQ Browser resolves decentralized domains without tracking, the MASQ VPN Network routes traffic through a peer-to-peer network with no central logging, and Timpi Search delivers independent search results free from hidden algorithms. Together, these features make privacy the default, not an afterthought, showcasing how zero-knowledge technology can power a seamless, privacy-first Web3 experience.
With the help of hardware acceleration, recursive proofs, and platforms like Polygon zkEVM, ZKPs are quickly transitioning from theoretical research to practical Web3 infrastructure. The potential is enormous - the only question is how quickly adoption will follow.
FAQs
Do ZK-proofs make blockchain transactions truly anonymous?
Zero-knowledge proofs (ZK-proofs) offer a strong layer of privacy for blockchain transactions by confirming the validity of information without revealing the actual data. This means sensitive details remain hidden while still proving the transaction's legitimacy. However, it's important to note that ZK-proofs alone don't ensure total anonymity. Certain metadata or contextual clues can still be exposed, leaving traces that could potentially be analyzed. To achieve complete anonymity, additional privacy measures beyond ZK-proofs are often necessary.
What’s the difference between zk-SNARKs and zk-STARKs for privacy?
The main distinction between zk-SNARKs and zk-STARKs comes down to their cryptographic foundations and the trade-offs they involve.
zk-SNARKs rely on elliptic curve cryptography and require a trusted setup to function. This approach results in smaller proofs and quicker verification times, making them efficient in certain scenarios.
On the other hand, zk-STARKs are built on hash functions, which means they don't need a trusted setup. They are also resistant to quantum computing threats. However, this comes at the cost of generating larger proofs and requiring more computational power.
Each method has its strengths, making them suitable for different Web3 applications focused on privacy and scalability.
How can ZK-proofs prove my identity without exposing my personal data?
Zero-knowledge proofs (ZKPs) make it possible to confirm your identity or credentials without exposing private details like your name or address. Using advanced cryptographic methods, ZKPs validate claims - like proving you're over a specific age - without disclosing the underlying data. This approach strengthens privacy in Web3 by allowing identity verification and transaction validation while safeguarding personal information.




