
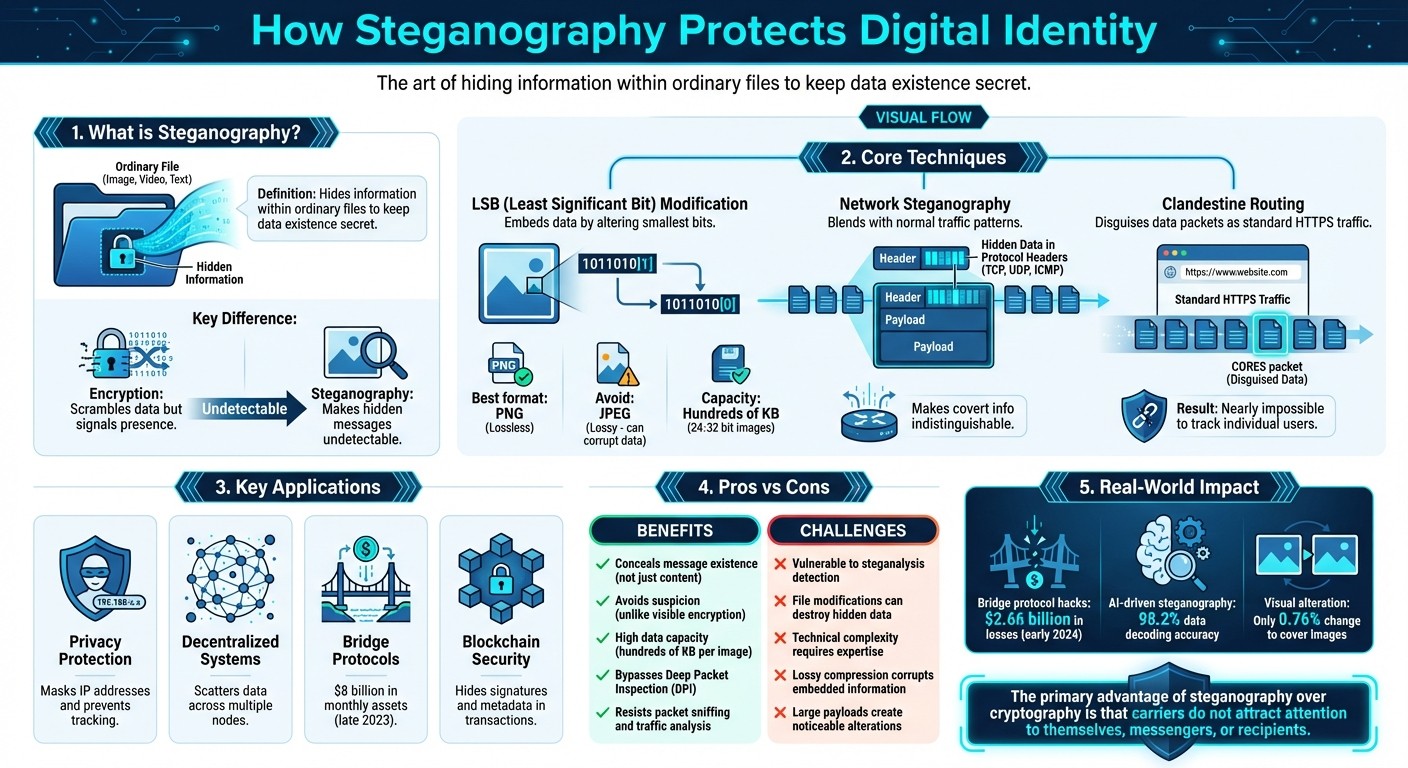
Steganography is the practice of hiding information within ordinary files like images, videos, or text to keep the existence of the data secret. Unlike encryption, which scrambles data but signals its presence, steganography ensures the hidden message remains undetectable. This makes it a powerful tool for safeguarding digital identities in today's cyber landscape.
Key Takeaways:
What It Does: Conceals sensitive data within everyday files or network traffic, making it invisible to attackers.
How It Works: Techniques like Least Significant Bit (LSB) modification embed data without noticeable changes to the carrier file.
Applications:
Protecting online activity by disguising IP addresses and blending data into normal network traffic.
Used in decentralized systems to secure communication by scattering data across multiple nodes.
Challenges: Vulnerable to detection via steganalysis, file modifications, and technical complexity.
Steganography is not just a defensive tool but also a method exploited by cybercriminals, as seen in incidents like the SolarWinds attack. Still, it plays a critical role in privacy tools like MASQ, which masks online activity to prevent tracking and surveillance. While it offers strong privacy benefits, its use requires careful implementation to avoid detection or data loss.
How Steganography Protects Digital Identity: Techniques and Applications
How Steganography Protects Digital Identity
Hiding Data with Steganographic Techniques
Steganography safeguards digital identity by embedding sensitive information into ordinary files, making the data's existence virtually invisible. Unlike cryptography, which encrypts data but signals its presence, steganography ensures the carrier file - whether it's an image, audio file, or document - looks completely unremarkable to anyone examining it.
A widely used method is the Least Significant Bit (LSB) technique. By subtly altering the smallest bits of digital data, this method can embed significant amounts of information without raising suspicion. For instance, in 24- or 32-bit digital images, hundreds of kilobytes of hidden data can be stored. To maximize security, it’s wise to encrypt the data before embedding it and to use lossless file formats like PNG. Lossy formats such as JPEG can unintentionally degrade or corrupt the hidden data due to their compression processes. Beyond file-level protection, steganography also plays a role in securing network interactions.
Masking IP Addresses and Preventing Tracking
Steganography isn't just limited to hiding information in files - it also enhances the security of network activity. Through network steganography, data is embedded into protocol headers like TCP, UDP, or ICMP, blending it seamlessly into normal traffic. This strategy makes covert information indistinguishable from regular network communication.
An advanced approach, known as clandestine routing, disguises data packets to mimic standard HTTPS traffic. MASQ, for example, uses this technique through its CORES (Client-Origin-Relay-Exit-Server) packets, which seamlessly integrate with everyday web activity.
"By disguising packets within normal traffic patterns, it deters typical packet sniffing and traffic analysis methods, and prevents the blocking of requests." - MASQ Network
This blending ensures that your online activity becomes nearly impossible to track. Since your traffic looks identical to millions of other HTTPS connections, it’s extremely challenging for censors or trackers to isolate individual users - or even recognize that privacy tools are being used.
Steganography in Decentralized Privacy Networks
How Decentralized Systems Use Steganography
Decentralized networks take steganography to the next level by distributing hidden data across multiple independent nodes. This setup ensures that even if part of the communication is intercepted, reconstructing the full message becomes a daunting task.
At the network level, embedding data within regular traffic adds another layer of security. Take "Stego-chain" as an example: it embeds data into images using advanced edge detection techniques, then encrypts and broadcasts these images in fragments across various nodes. Even if someone intercepts one of these stego-images, the decentralized nature of the system makes tampering or decryption incredibly challenging. Decentralized networks also create covert channels on public ledgers, where steganography hides signatures, watermarks, or sensitive metadata within blockchain transactions.
As of late 2023, bridge protocols were moving over $8 billion in assets monthly, but leaked metadata could still reveal user identities. With bridge hacks resulting in $2.66 billion in losses by early 2024, the urgency for steganographic protection is clear.
"Steganography attempts to hide a message within another object... it also seeks to conceal that a message is being sent in the first place." - David Tidmarsh, EC-Council
By scattering sensitive data across decentralized nodes, steganography strengthens defenses against tracking and surveillance. These techniques are the backbone of integrated privacy tools like MASQ.
How MASQ Uses Steganography for Online Privacy
MASQ builds on decentralized steganographic methods to protect digital identities through multiple layers of anonymity. Its decentralized architecture uses steganography to disguise data packages, making them look like everyday web traffic - whether that’s HTTPS browsing, video streaming, or file downloads. This approach hides not just the content but also the very use of privacy tools.
By blending data streams from numerous users in a peer-to-peer network, MASQ makes it nearly impossible for outsiders to trace individual activities. Unlike centralized VPNs, MASQ’s distributed system ensures no single node has a complete picture of your online behavior. Each hop in the multi-layered routing adds another layer of encryption, while steganographic masking helps bypass Deep Packet Inspection (DPI), which is often used to detect and block specific types of traffic.
"Because traffic patterns viewed over time can be distinguishable... masking packages in random traffic patterns can deter typical packet sniffing and network traffic analyzation methods." - MASQ Network
Pros and Cons of Steganography for Digital Identity Protection
Benefits of Steganography
One of the standout features of steganography is its ability to conceal not just the content but also the very existence of a message. This makes it far less likely to draw attention compared to encryption, where scrambled text can raise suspicion. Instead of transforming a message into an unreadable format, steganography hides it within seemingly ordinary files, like images or videos, making it appear harmless to censors, internet service providers, or monitoring systems. As Michael Brian Pope from Mississippi State University puts it:
"The primary advantage of steganography over cryptography is that the carriers do not attract attention to themselves, to messengers, or to recipients".
Advanced techniques, such as embedding data within regular traffic like video streams or HTTPS flows, add another layer of protection. This approach helps avoid detection by tools like packet sniffers or Deep Packet Inspection systems. Additionally, the data capacity of steganographic methods is surprisingly high. For example, a single high-resolution image can hold hundreds of kilobytes of hidden data using Least Significant Bit (LSB) encoding. This method subtly alters pixel values in a way that is imperceptible to the human eye, ensuring the message remains secure - even when combined with encryption.
Drawbacks and Challenges
Despite its strengths, steganography is not without its challenges. Specialized tools for steganalysis can identify patterns, unusual metadata, or inconsistencies that might reveal hidden data. Techniques like LSB steganography are particularly vulnerable to file modifications. Actions such as resizing, editing, or converting files to lossy formats (like JPEG) can easily erase the hidden information.
Another hurdle is the technical complexity involved. Concealing data within network protocols like TCP, UDP, or ICMP requires advanced skills, and even small implementation errors can compromise the hidden data. There's also an ethical concern: while steganography can protect journalists and activists from surveillance, it can also be misused to hide malware or facilitate unauthorized data transfers.
Challenge | Impact | Mitigation |
|---|---|---|
Steganalysis Detection | Automated tools can spot statistical anomalies in data | Combine with encryption and apply advanced masking techniques |
File Manipulation | Editing or compressing files can destroy hidden messages | Use lossless formats like PNG and avoid re-encoding |
Limited Capacity | Large payloads may create noticeable alterations | Restrict payload size and spread data across multiple files |
High Complexity | Network steganography requires specialized knowledge | Use tools like MASQ to simplify and automate the process |
Steganography - Science of Hidden Communication by Suraj Pandey I IdentityShield Summit ‘24
The Future of Steganography in Digital Privacy
Steganography is evolving beyond traditional methods like Least Significant Bit (LSB) embedding, thanks to advancements in AI. Deep learning techniques, such as Convolutional Neural Networks (CNNs) and Generative Adversarial Networks (GANs), are driving the development of adaptive data-hiding methods that closely resemble the statistical patterns of cover files. Research indicates these AI-driven approaches achieve impressive results, offering near-perfect visual fidelity and accurate text recovery. This progress not only improves data-hiding techniques but also enhances network-level obfuscation.
One such innovation is clandestine routing, which disguises data packets as random web traffic to thwart packet sniffing and traffic analysis. According to MASQ Network:
"Each CORES package will be wrapped in a layer of obscurity that will resemble different types of traffic... to deter typical packet sniffing and traffic analysis methods, and prevents the blocking of requests".
This makes it significantly harder for internet service providers or censors to detect the use of privacy tools, providing an essential complement to existing steganographic practices.
Newer models also enhance data capacity while maintaining the integrity of cover files. By combining lossless compression with deep learning, these systems increase payload capacity without compromising security. For example, research into "StegNet" models has shown a data decoding accuracy of 98.2%, with only a 0.76% alteration to the average cover image. These advancements allow for larger amounts of hidden data while preserving the visual quality of the medium.
Additionally, advanced multi-hop routing techniques further isolate user traffic. When paired with emerging technologies like Oblivious HTTP (OHTTP) and protocol mimicry through uTLS, these innovations pave the way for a more private internet. Such tools are designed to resist automated detection and even state-level censorship. Together, these advancements build on and extend the decentralized privacy approaches already in use today.
FAQs
What’s the difference between steganography and encryption in protecting your digital identity?
Steganography and encryption are both powerful tools for safeguarding digital information, but they take very different approaches.
Encryption works by transforming data into a scrambled, unreadable format. Without the correct decryption key, the data remains inaccessible, ensuring that even if someone intercepts it, they can’t understand it. This method is all about maintaining confidentiality.
Steganography, in contrast, doesn’t just protect the content - it hides its very existence. It embeds data within ordinary files, like images or audio, making it nearly invisible. For instance, a photo might secretly contain a message, and unless you know where to look, you’d never know it’s there.
The key difference lies in their goals: encryption guards sensitive information from being accessed, while steganography avoids detection entirely. Interestingly, these techniques can complement each other. Imagine a scenario where a hidden message inside an image is also encrypted - this creates a double layer of security, making it both undetectable and unreadable to outsiders. Together, they provide a robust defense against cyber threats.
What are the potential risks of using steganography for protecting your digital identity?
Steganography, while useful for safeguarding privacy by embedding information into everyday files, carries some serious risks. Cybercriminals can exploit this method to conceal malware, spyware, or stolen data within files like images or videos. These hidden threats often slip past traditional security tools, potentially leading to data breaches, unauthorized access, or compromised systems.
Another concern is its use in covert communication by malicious actors, which complicates efforts to maintain cybersecurity. With advanced techniques, including AI-driven methods, detecting hidden data becomes even more challenging, increasing the likelihood of successful attacks. To counter these risks, it's essential to pair steganography with robust cybersecurity measures, like advanced monitoring and detection tools, to better protect digital identities.
How do decentralized networks improve the effectiveness of steganography?
Decentralized networks bring a new level of sophistication to steganography by utilizing a peer-to-peer (P2P) structure that makes tracking or intercepting data significantly more challenging. Unlike centralized systems that depend on a limited number of servers - making them easier targets - decentralized networks distribute traffic across numerous independent nodes. Many of these networks also use multi-hop encryption, which adds layers of protection by obscuring communication paths.
These networks often incorporate advanced techniques like traffic obfuscation and mixnets. Traffic obfuscation disguises data flows, while mixnets shuffle data packets between nodes, making it nearly impossible for anyone to perform deep packet inspection or analyze traffic patterns effectively. The result is a system that not only resists censorship and surveillance but also allows hidden messages to blend seamlessly into everyday internet activity. Platforms like MASQ take this a step further by integrating Web3 tools and encrypted routing, offering enhanced privacy and security for users seeking digital anonymity.




